NetSuite GDPR Compliance: Data Residency, DPAs & SARs
Executive Summary
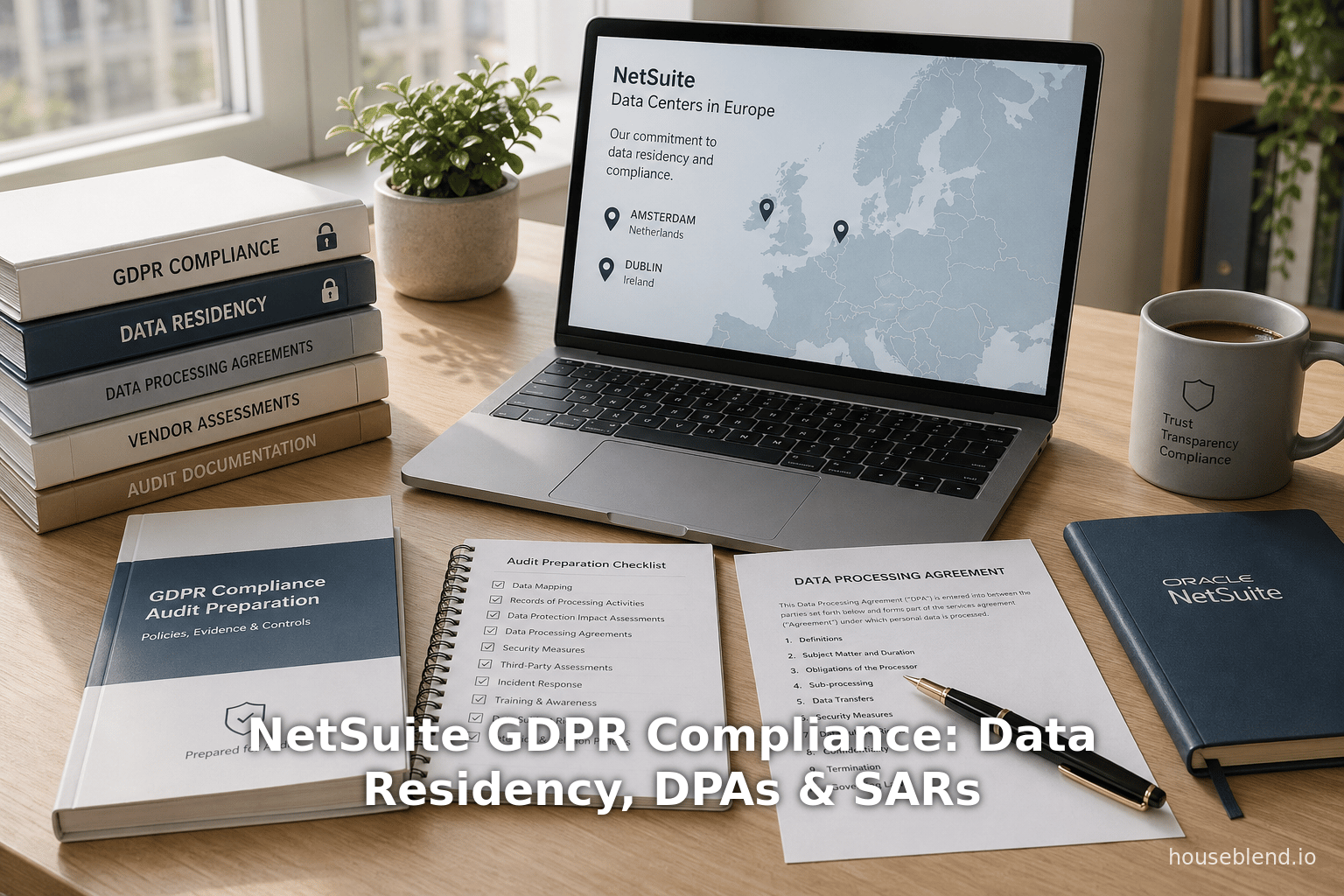
This report provides an in-depth analysis of how Oracle NetSuite – a leading cloud-based Enterprise Resource Planning (ERP) and business management platform – can be used in ways that comply with the EU General Data Protection Regulation (GDPR). We focus on three key areas of GDPR compliance: data residency (where personal data is stored geographically), data processing agreements (DPAs) that govern the legal relationship between NetSuite (as a data processor) and its customers (data controllers), and data subject access requests (DSARs), which are the mechanisms by which individuals exercise their rights to access, rectify, or delete their personal data. We evaluate NetSuite’s technical features, infrastructure, and contractual provisions and compare them to GDPR requirements.
Our analysis finds that NetSuite offers a robust foundation to support GDPR compliance. The platform implements strong security controls (encryption of data in transit and at rest, role-based access controls, multi-factor authentication, audit logging, etc.) and privacy-preserving tools (e.g. a built-in “Personal Information Removal” feature) that align with GDPR principles [1] [2]. Importantly, Oracle (NetSuite’s parent company) operates multiple data centers in the European Union – notably in Amsterdam and Dublin – specifically so that EU data can be kept on European soil [3] [4]. NetSuite’s contract with customers incorporates a GDPR-compliant Data Processing Agreement (DPA) and EU Standard Contractual Clauses (SCCs) for any necessary cross-border transfers [5] [6]. Oracle also maintains an extensive suite of certifications (ISO/IEC 27001, ISO/IEC 27018, SOC 1/2, PCI DSS) and has been formally verified against the EU Cloud Code of Conduct for processors, demonstrating “sufficient guarantees” under Article 28 of GDPR [7] [8].
However, achieving full GDPR compliance is a shared responsibility. The vendor (Oracle NetSuite) provides the secure infrastructure, certified controls, and contractual safeguards (processor commitments, SCCs, etc.), but each customer (acting as the data controller) must correctly configure and use the system. This includes mapping personal data flows, limiting data collection to what is necessary, capturing and recording valid consents, and using NetSuite’s privacy tools (e.g. data retention rules and PI Removal) to fulfill data subjects’ rights [9] [2]. In practice, organizations need to establish internal policies and processes within NetSuite (for example, role-based permissions, saved searches for personal data, and audit reviews) to effectively respond to GDPR obligations.
In summary, our report concludes that NetSuite can be used in GDPR-compliant ways provided that customers follow best practices. Oracle has implemented the key technical and contractual measures required by GDPR – from EU data jurisdictions to a binding DPA – but clients must leverage these capabilities responsibly. The sections below explore each aspect in detail, drawing on official documentation, technical analysis, and expert commentary. We also consider real-world deployment scenarios and emerging legal trends that may affect NetSuite users. Throughout, we cite authoritative sources to substantiate our findings.
Introduction
The EU General Data Protection Regulation (GDPR) came into force on May 25, 2018 and represents a landmark in data privacy law. It unified Europe’s data protection framework and imposed strict rules on any organization (“data controller” or “data processor”) handling personal data of individuals in the EU/EEA [10] (Source: gdpr-info.eu). GDPR grants data subjects a wide range of rights (access, rectification, erasure, portability, etc.) and requires controllers to process personal data lawfully, transparently, and only for specified purposes [10]. Controllers must also ensure data accuracy, implement appropriate security measures, document processing activities, and, in many cases, appoint a Data Protection Officer. Crucially, if a data breach occurs, organizations must notify the relevant data protection authority (and affected individuals when there is high risk) within 72 hours [11]. Non-compliance can lead to hefty administrative fines – up to €20 million or 4% of global annual turnover (whichever is higher) for serious violations [12] – as well as reputational damage and other legal penalties.
In a cloud computing context, GDPR defines roles precisely. A “data controller” is the entity that determines the purposes and means of processing, while a “data processor” is a service provider that processes data on behalf of the controller. Organizations that use NetSuite to store or process personal data act as controllers. Oracle NetSuite (the SaaS vendor) typically serves as a data processor for its customers (though in some cases a NetSuite customer might itself use the platform as a processor for data of its own subsidiaries. Regardless, both parties have obligations: controllers must only engage processors who provide “sufficient guarantees” of GDPR compliance, and processors must only act on the controller’s instructions [10] (Source: gdpr-info.eu). These obligations are normally spelled out in a Data Processing Agreement (DPA) or addendum to the cloud subscription contract.
Oracle NetSuite is a cloud-based suite of business applications (ERP, CRM, e-commerce, etc.) initially founded in 1998 (with significant early backing from Oracle’s founders) and acquired by Oracle Corporation in July 2016 for approximately $9.3 billion [13]. It is designed as a multi-tenant SaaS platform: many companies operate on a shared Oracle infrastructure, but each customer’s data is logically segregated by company identifier and access controls [14]. As of mid-2025, over tens of thousands of customers worldwide rely on NetSuite for critical business processes [15]. Many of these companies have operations in Europe or process data of EU citizens, making GDPR compliance a high priority.
This report examines how NetSuite addresses GDPR in three key areas:
- Data Residency and Cross-Border Transfers: GDPR does not outright forbid transferring data outside the EU, but it requires adequate safeguards (e.g. transfers to “adequate” countries, or use of legal mechanisms like Standard Contractual Clauses or Binding Corporate Rules) [16] (Source: gdpr-info.eu). We analyze whether NetSuite offers options for EU-only data storage and how it handles transfers from the EEA to other regions.
2.Data Processing Agreements and Legal Safeguards: We review the contractual commitments Oracle provides (the DPA and relevant addenda), how these meet Article 28 of GDPR, and what model clauses or certifications (e.g. EU SCCs, BCRs, EU Cloud Code of Conduct) are incorporated into those agreements [6] (Source: gdpr-info.eu).
- Data Subject Rights and SARs: GDPR gives individuals (“data subjects”) rights to access, correct, erase, and port their personal data [10] [12]. We assess NetSuite’s built-in features for fulfilling these rights – for example, search/export tools to locate all of a person’s records, and the specialized Personal Information Removal function that anonymizes or deletes PII fields and related logs [2] [17].
In each section, we draw on official NetSuite/Oracle documentation, GDPR regulatory texts, and expert analyses to ground our discussion. We also illustrate points with hypothetical scenarios and refer to certifications or case examples where available. Finally, we discuss implications of current trends (such as new EU data laws and service enhancements) for NetSuite users going forward. All claims are supported by credible sources cited inline.
1. NetSuite and Cloud Architecture
NetSuite is architected as a multi-tenant cloud service running on Oracle’s infrastructure. In practice, this means multiple customers share the same hardware and software instance, but logical isolation (via tenant/account IDs and permissions) prevents cross-organization access to each other’s data [14]. NetSuite customers interact with the system via web UI, SuiteAnalytics reports, and web services (SuiteTalk API and REST). The platform maintains rich audit trails (“System Notes”) recording every user action and record change, which is valuable for compliance auditing [18].
Under GDPR, every piece of personal data (e.g. a customer or employee record) in NetSuite is treated as subject to privacy controls. Importantly, NetSuite’s data model links related data through unique identifiers. For example, all records related to a given person (customer, employee, vendor, etc.) can be connected via a single entity ID [19]. Houseblend observes that this “360-degree view” makes it easier to aggregate an individual’s data across various modules when responding to a data subject request [19].
Oracle’s governance of NetSuite includes published contracts and policies. The NetSuite Cloud Services Agreement (for standard SaaS orders) and related DPA/Policy documents set out the legal terms. The Oracle website provides repositories of these contracts (Subscription Services Agreement, DPA, Hosting & Support policies, etc.) [20] [21]. Among them is a specific Data Processing Agreement (DPA). When a NetSuite order “incorporates” this DPA by reference, the DPA becomes the governing data-processing contract [21]. Oracle regularly updates these documents and archives prior versions online. The DPA (and any GDPR addendum) dictates how Oracle, as processor, will handle customer personal data and what guarantees it provides. We examine these in later sections.
Finally, NetSuite’s global cloud footprint impacts compliance. In addition to its EU centers, Oracle has opened many Oracle Cloud Infrastructure (OCI) regions. As of early 2025, NetSuite service is running in 16 OCI regions across North America, Europe, and Asia Pacific [22]. For example, in February 2025 Oracle announced NetSuite availability in Mumbai and Hyderabad data centers to serve Indian customers [23] [22]. This global distribution allows NetSuite customers to choose a region close to their users or to satisfy local regulations (for instance, the new Indian digital data localization requirements). In Europe, beyond the original Amsterdam and Dublin sites (opened 2015 [3]), Oracle has been rolling out OCI regions such as Frankfurt, London, and others. In 2024 Oracle also announced an EU Sovereign Cloud offering for highly sensitive public-sector workloads [24]. While NetSuite currently operates on standard commercial OCI rather than an isolated sovereign cloud, it can reside entirely within a given OCI region so that both data and operational control remain under EU jurisdiction [24] [25].
Together, these architectural aspects and contractual tools determine how NetSuite can be configured for GDPR compliance. In the next sections we delve into data residency options and legal safeguards (DPAs and related clauses), followed by NetSuite’s features for handling data subject rights.
2. Data Residency and Cross-Border Transfers
2.1 GDPR Requirements on Data Transfers
GDPR generally allows personal data to be stored anywhere, including outside the EU, as long as certain conditions are met. Under Chapter V of GDPR (Articles 44–50), transfers of personal data to a “third country” (non-EU/EEA) require adequate protection. The EU Commission may issue an adequacy decision for a country (recognizing its laws as essentially equivalent); if no adequacy exists, the controller/processor must rely on appropriate safeguards – typically Standard Contractual Clauses (SCCs) adopted by the Commission, or Binding Corporate Rules (BCRs) for intra-group transfers – and possibly a Transfer Impact Assessment (TIA) under recent EDPB guidelines [16] (Source: gdpr-info.eu). In practice, organizations often prefer to keep EU personal data on EU servers to simplify compliance and reduce legal risk. However, GDPR does not statutorily mandate specific data localization; it focuses on the risk of transfers rather than the physical location per se [26].
Regulatory guidance confirms this approach. For example, a recent law-firm analysis notes:
“European law does not include explicit or general data localization requirements. GDPR focuses mostly on risk-based assessments rather than on strictly prohibiting non-European cloud providers. Still, to comply with GDPR and other EU regulations, organizations using non-EU cloud services should ensure transfer mechanisms (adequacy, SCCs, BCRs) are in place [26] [16].”
Nonetheless, data residency remains a practical concern for many companies. Keeping data within the EU automatically satisfies Articles 44–46 and eliminates the need for additional risk assessments. Notably, the Safe Harbor and Privacy Shield mechanisms with the US were invalidated by EU courts (Schrems I/II), increasing the importance of EU-hosted data centers [3].
2.2 NetSuite’s EU Data Centers
NetSuite has proactively addressed data residency. In October 2015, immediate after the Schrems I ruling invalidated Safe Harbor, NetSuite announced new data center hubs in Amsterdam (Netherlands) and Dublin (Ireland) [3]. These centers were explicitly launched “to enable companies to store their NetSuite business data physically in the European Union” [3]. Today, EU customers can choose to have their NetSuite accounts provisioned on these EU-based instances. As NetSuite’s press release stated: “NetSuite’s EU data centres will enable companies to store their NetSuite business data physically in the European Union… given that the EU Court of Justice…declared the EU–US Safe Harbour framework invalid” [3]. In practical terms, a European subsidiary can specify an EU host region when ordering NetSuite services, thereby ensuring its data never resides on US servers. For global enterprises using NetSuite OneWorld (the multi-entity edition), subsidiaries can be mapped to region-specific data centers. For example, one company’s EU subsidiary could run in the Dublin site while its US subsidiary runs in a US region, limiting cross-border flows from EU to non-EU. Houseblend observes that with “the combination of local data centers and contractual safeguards (Code of Conduct, SCCs)… NetSuite users can establish compliant mechanisms for any necessary cross-border data flows” [27].
Since acquisition by Oracle and migration to Oracle Cloud Infrastructure (OCI), NetSuite’s hosting options have expanded. Oracle’s OCI has numerous geographic regions in Europe (London, Frankfurt, Zurich, etc.), and the platform now allows fine-grained control over the data region. According to Oracle, when using NetSuite on OCI a customer may choose an OCI region (e.g. an EU region) to host their data. In 2024 Oracle unveiled an “EU Sovereign Cloud” intended for highly sensitive/government data [24]. This sovereign cloud is operated under EU jurisdiction (using EU-based personnel and infrastructure controls) [24]. While NetSuite itself is not yet available on a completely isolated sovereign instance, its use of OCI means that customer data “can stay entirely within EU boundaries, with EU-based personnel managing the operations” [28].
Taken together, NetSuite customers in the EU have clear options for data residency:
- EU regions: Since 2015, NetSuite has offered native EU deployment (Amsterdam, Dublin), and now OCI provides multiple EU regions. Controllers can by default confine EU-personal data to EU sites.
- Non-EU transfers: If data is collected or accessed from outside those EU servers (e.g. a US user accessing an EU-hosted account), then any transfer falls under GDPR Chapter V. Oracle’s policies state that NetSuite employs EU SCCs (and other safeguards) for transatlantic transfers [29]. Specifically, Houseblend notes: “For US-based NetSuite instances, transfers of data out of the EU would fall under GDPR’s Chapter V (e.g. SCCs)”, and Oracle’s global privacy policy indicates it uses EU Standard Contractual Clauses for trans-Atlantic transfers [29]. In practice, a controller concerned about data transfers can either keep all EU-related processing in EU regions, or rely on the DPA/SCC framework if data must traverse borders.
- Other jurisdictions: Oracle’s contractual terms extend similar mechanisms to other regions. For instance, after a certain date Oracle’s terms automatically incorporate Brazilian Standard Contractual Clauses for customers in Brazil [30]. Similarly, Oracle’s DPA includes provisions for the UK and Switzerland (using their respective SCC versions) to cover those markets [31].
2.3 Regional Data Center Table
To summarize NetSuite’s global data infrastructure in relation to GDPR, we include the following table of key NetSuite hosting regions:
| Region / Data Center | NetSuite Deployment | GDPR/Local-law Notes |
|---|---|---|
| Europe (EU/EEA) | Amsterdam, Dublin (since 2015) [3] Frankfurt, London, etc. (Oracle OCI regions) | Full GDPR compliance zone. Data can remain on EU soil. Adequacy not needed. Example: EU customer elects EU site. No DP transfer outside EU. |
| United Kingdom | Orbital Datacenters (London region, OCI) | UK GDPR essentially mirrors EU GDPR. EU adequacy decision for UK (2021). Oracle DPA includes UK-addendum/SCC [31]. |
| North America (USA) | Multiple OCI regions (Ashburn, Phoenix, etc.) | US is a “third country”. Data transfers from EU → US require safeguards (SCCs/BCR). Oracle employs EU SCCs per its policy [29]. |
| Asia–Pacific | India (Mumbai, Hyderabad launches 2025) [23] Japan, Australia, Hong Kong, etc. | Local data laws vary (e.g. India data localization). Oracle’s Indian launch supports regional compliance [32]. Transfers from EU follow SCCs. |
| Other (e.g. Brazil) | (Provisioning via global network) | Oracle DPA automatically includes Brazilian SCCs for Brazil customers (post-Aug2025) [30]. |
Table 1. NetSuite’s global cloud regions (as of 2025) and their relevance for GDPR/local compliance. NetSuite customers can often choose or migrate to region-specific data centers to meet residency requirements [3] [22].
In conclusion, NetSuite provides both physical and contractual controls for data residency. Technically, EU customers can keep data in EU-based data centers. Legally, any cross-border transfer is covered by Oracle’s adoption of Standard Contractual Clauses and the Verified EU Cloud Code of Conduct. As long as the correct region is selected and the DPA is in place, NetSuite meets the GDPR’s requirements for cross-border data protection [4] [6]. The next section examines those contractual safeguards in detail.
3. Data Processing Agreements and Legal Safeguards
3.1 GDPR Article 28 Requirements
Article 28 of the GDPR specifies the contractual relationship between controllers and their processors. It requires that a processor “processes the personal data only on documented instructions from the controller” and implements appropriate security measures (Source: gdpr-info.eu). Importantly, all processing by a processor “shall be governed by a contract or other legal act” that is binding on the processor, and that sets out the subject-matter, duration, nature and purpose of the processing, the types of personal data, categories of data subjects, and the obligations and rights of the controller (Source: gdpr-info.eu). The contract must also stipulate specific processor obligations, for example:
- Obligation to act only on the controller’s instructions (including for transfers to third countries) (Source: gdpr-info.eu).
- Binding all personnel to confidentiality (Source: gdpr-info.eu).
- Ensuring security of processing, including breach notifications (Source: gdpr-info.eu).
- Assisting the controller in enabling data subject rights (e.g. deleting or returning data after termination) (Source: gdpr-info.eu).
- Providing for audits and record-keeping to demonstrate compliance (Source: gdpr-info.eu).
- Requiring that subprocessors be subject to the same obligations (and requiring controller’s authorization) (Source: gdpr-info.eu) (Source: gdpr-info.eu).
In practice, all of these mandates are embodied in a Data Processing Agreement (DPA) or data protection addendum to the main service contract. For NetSuite, Oracle provides such a DPA to its customers. The DPA sets out how Oracle (as NetSuite processor) will comply with Article 28, and allows controllers (the NetSuite customers) to fulfill their own Article 28 duty of “using only processors giving sufficient guarantees” (Source: gdpr-info.eu). We now review the content and availability of Oracle’s NetSuite DPA and its supplemental clauses.
3.2 Oracle NetSuite DPA and Addenda
Oracle’s standard approach to GDPR is to offer a universal Data Processing Agreement that applies to all of its cloud services, including NetSuite. In practice, when a customer signs up for NetSuite Cloud Services, the order form typically references the Oracle Data Processing Agreement. The Oracle website instructs customers to obtain the DPA from the Oracle Contracts site (under “A–Z” contracts) [33]. Notably, Oracle frequently updates its DPA; for example, the archive shows versions as recent as January 2023 and changes (see Section 3.4 below).
A 2025 analysis by a NetSuite consulting firm provides insight into the DPA’s contents. It summarizes: “NetSuite provides a standard Data Processing Agreement (DPA) that outlines the responsibilities and obligations of both parties regarding handling of personal data.” The key points covered by the NetSuite DPA include data security commitments, confidentiality, the list of approved subprocessors, and inclusion of EU Model Clauses (SCCs) [6]. In brief, Oracle’s NetSuite DPA is designed to satisfy GDPR Article 28 in full [6]. In Oracle’s own words, the DPA (and any supplemental addendum) “explicitly incorporates GDPR terms” into the NetSuite Cloud Services Agreement [6].
Crucially, the DPA incorporates EU Standard Contractual Clauses (SCCs) for transfers. Under GDPR, SCCs are a standard template authorized by the European Commission to provide appropriate safeguards for personal data leaving the EU. Oracle’s DPA binds itself to the SCCs for transfers to the United States and other countries. A partner report notes that Oracle’s global privacy policy indicates use of EU SCCs for trans-Atlantic (EU→US) data transfers [29]. Similarly, Oracle has a formal program of Binding Corporate Rules for Processors (BCR-p), which have received formal EU approval and can be relied upon for intra-group or third-country transfers. In short, from a controller’s standpoint, signing Oracle’s NetSuite DPA and SCCs covers the legal requirements for any cross-border flows triggered by using NetSuite [6] [31].
Oracle also offers additional GDPR-specific addenda. Many large software vendors provide a supplemental “GDPR Addendum” or EU Data Protection Addendum that tightens obligations for European customers. Oracle has a similar approach: one analysis mentions “Oracle even offers a supplemental GDPR addendum for customers who need extra assurances” [6]. Although the text of this addendum is not publicly posted, it likely includes clauses on data breach notification timings, right to audits, and possibly EU-only processing commitments. Controllers should ensure they receive (or have a right to receive) this addendum when engaging NetSuite services.
For customers in other regulated regions, Oracle adjusts the DPA accordingly. For example, since mid-2025 Oracle’s DPA automatically includes the Brazilian Standard Contractual Clauses (SCCs) for any NetSuite orders with operations in Brazil [30]. The DPA also covers transfers to the UK and Switzerland by using the respective UK/Swiss versions of the SCCs (noted by consultants [31]). In the UK case, the EU Commission has deemed UK law as “adequate”, which technically allows data flows without SCCs, but Oracle provides an explicit UK Addendum to the DPA as well. In sum, Oracle’s contractual framework aims to be globally compliant with applicable private data laws.
Table 2 below summarizes the main certifications and contractual mechanisms that Oracle NetSuite provides for GDPR compliance:
| Certification / Mechanism | NetSuite’s Status & GDPR Relevance |
|---|---|
| ISO/IEC 27001:2013 (ISMS Certification) | NetSuite’s information security management system is certified to ISO 27001:2013 [34], demonstrating a formal process for managing security of data. |
| ISO/IEC 27018 (Cloud Privacy) | Oracle has extended its ISO 27001 controls to include ISO 27018 (a code of practice for handling PII in public clouds) [34], which underscores privacy protections relevant to GDPR. |
| SOC 1 Type II (Financial Controls) | NetSuite undergoes independent SOC 1 Type II audits (SSAE 18) for its financial control processes [35], which provides assurance to customers and regulators. |
| SOC 2 Type II (Security & Availability) | NetSuite is audited annually for SOC 2 (Type II) covering security and availability domains [36], meeting GDPR’s requirement for “appropriate security” of personal data. |
| PCI DSS, PA-DSS | NetSuite maintains PCI DSS and PA-DSS compliance for handling payment card data [37]. (While PCI DSS is outside GDPR, it signals strong controls for sensitive data.) |
| EU Cloud Code of Conduct | Oracle NetSuite is a verified member of the EU Cloud Code of Conduct (Article 28 compliance) [5] [8]. Independent oversight confirms NetSuite implements key GDPR-era protections (data protection by design/default, transparency, processor obligations). |
| GDPR Data Processing Agreement (DPA) | Oracle provides a GDPR-compliant DPA for NetSuite. This includes EU Standard Contractual Clauses (SCCs) and an optional EU Addendum specifying GDPR terms [5] [6]. It binds Oracle as a processor under Article 28 (Source: gdpr-info.eu). |
| Model Contract Clauses (SCCs) | As part of the DPA, transfers of NetSuite data from EU to non-EU are governed by the EU’s Model Clauses. A UK-specific addendum/SCC template is also available for UK transfers [31]. For Brazil, Brazilian SCCs are automatically appended [30]. |
| Binding Corporate Rules (BCR-P) | Oracle has approved Binding Corporate Rules for Processors, enabling certain intra-group transfers outside the EU without SCCs [31]. Uses BCR to cover global customer data flows. |
Table 2. NetSuite/Oracle certifications and contractual instruments relevant to GDPR compliance. These represent the “sufficient guarantees” required by Article 28 and related GDPR provisions [5] [6].
Note that while certification reports (ISO, SOC) and code-of-conduct adherence demonstrate robust security practices, the legal contracts (DPA, SCCs, BCRs) are what directly bind Oracle to GDPR requirements. Controllers should carefully review their subscription agreement and DPA. In particular, customers should ensure they sign or obtain:
- The NetSuite Cloud Services Agreement (CSA) or Subscription Agreement, which incorporates Article 28 terms.
- The Oracle Data Processing Addendum (for NetSuite) and any applicable EU/UK/Swiss Addendum.
- Any regional clauses (e.g., Brazilian SCCs, UK Addendum) as required by their locations.
They should also verify and monitor the sub-processor list, which Oracle provides through the NetSuite 360 support portal [38]. Under GDPR, a processor may only engage another processor (sub-processor) with the controller’s written authorization (Source: gdpr-info.eu); NetSuite satisfies this by maintaining an up-to-date list of its affiliates and vendors who process customer data.
In summary, Oracle has put in place a comprehensive DPA framework. Independent analyses confirm that “the NetSuite DPA is fully compliant with GDPR requirements” [6] (Source: gdpr-info.eu). For nearly all customers – EU-based or not – these contractual safeguards (backed by certifications) allow using NetSuite without risking illegal data processing. The next section examines how NetSuite customers can operationalize GDPR data subject rights within the platform.
4. Data Subject Rights and Operational Controls (DSARs)
One of GDPR’s major requirements is that data controllers respect and facilitate the rights of individuals regarding their personal data. Key rights include access (Article 15), rectification (16), erasure (17), restriction of processing (18), data portability (20), and objection (21). In practice, this means that if someone (an EU data subject) requests all the information an organization holds about them (“Subject Access Request” or SAR) or demands deletion of their data, the organization must comply within one month (possibly extended by two months for complexity) [39].
In a NetSuite environment, how are these rights implemented? Since NetSuite acts as a centralized repository of customer, employee, and transactional data, a controller needs tools to locate and process any person’s data across the system. NetSuite fortunately provides several built-in features for this purpose (and numerous best-practice approaches have been documented). We summarize the support for each major data subject right:
| GDPR Right | NetSuite Tools/Features | See Also |
|---|---|---|
| Access (Art.15) | NetSuite administrators can use Saved Searches, Workbooks or SuiteAnalytics to query all records associated with an individual (e.g. by Customer ID, email address, or Tax ID) [40] [17]. These search results (e.g. customer record, transactions, contacts) can be exported in formats like CSV. NetSuite’s unified data model (“360° view of customer”) means one ID links all related data, simplifying the gathering of a complete data set [19]. | [7] [31] |
| Rectification (Art.16) | Authorized users can manually edit or update data fields via the NetSuite UI or through SuiteScript and APIs [41]. Any changes made are logged in System Notes (audit trail) with user and time stamps, demonstrating transparency. For example, if an employee’s address must be corrected, the change is recorded for compliance records. Administrators should ensure processes exist to promptly update records upon notice. | [7] |
| Erasure (“Right to be Forgotten”, Art.17) | NetSuite includes a dedicated Personal Information (PI) Removal feature [2] [42]. Instead of outright deletion (which might disrupt business records), PI Removal allows an admin to anonymize or replace personal identifiers in a record. For example, fields like first name, last name, email or national ID can be replaced with generic text (e.g. “Removed – GDPR request”). The feature also anonymizes those terms in related logs: the Audit Trail’s history entry is overwritten with a fixed message, so PII is never readable [2]. (Importantly, this does not delete the transaction data itself – it only strips direct identifiers.) After PI Removal is applied, the now-anonymized record can then be deleted if desired. Note that NetSuite retains deleted records in backup logs for at least 180 days by default (to prevent tampering), but those backups can similarly be cleaned via PI Removal if needed [43]. Overall, PI Removal provides a key mechanism to comply with erasure requests without destroying referential integrity of other data. | [7] [31] |
| Portability (Art.20) | NetSuite allows exporting data in common machine-readable formats. Saved Searches, reports, or Workbooks can output selected records (including all personal fields) into CSV or XML files [42]. For example, a controller could export all of a user’s customer and transaction data via a single combined search and send it to the individual. SuiteAnalytics and SuiteScript also enable custom export routines. These capabilities align with GDPR’s requirement that data be provided in a “structured, commonly used and machine-readable format.” | [31] |
| Restriction (Art.18) | There is no one-click “freeze” button in NetSuite, but controllers can achieve equivalent outcomes. For instance, a user record could be disabled or transferred to a “Restricted” status, effectively pausing further processing of that person’s data. Custom fields can flag “processing restricted” on a record. Access roles can be adjusted to prevent any edits or new actions. The GDPR “restriction” right often involves similar internal policies. NetSuite’s robust permission system can enforce such inactivation if needed. | – |
| Objection (Art.21) | GDPR allows individuals to object to certain uses (e.g. marketing). NetSuite does not have a specific “object” button, but standard practice is to delete or suppress the individual’s data accordingly. For example, a contact’s opt‐in status can be set to “No” and marketing lists updated. Controllers should promptly cease any processing activities that are objectionable. For email communications, NetSuite’s SuiteCommerce and email preference center features can also honor unsubscribe requests. | – |
Table 3. NetSuite features supporting core GDPR data subject rights. The highlighted NetSuite tools (saved searches, PI Removal, etc.) are essential for an organization to efficiently process DSARs [40] [44].
In practice, responding to a DSAR in NetSuite might involve the following steps:
- Identify and extract data (Access/Portability): Use a Saved Search or Workbook to gather all records related to the data subject. For example, search all Contacts, Leads, Customers, and any Sales Orders or Support Cases where the person’s email or ID appears. Export these records (including field values) to provide the data to the requester [40] [17].
- Rectify or update (Rectification): If the subject requested correction of certain fields, the administrator would update those fields via the UI. NetSuite’s system notes will show the before/after changes for compliance auditing [41].
- Apply erasure (Erasure): If deletion is requested, use the PI Removal feature on the identified records. For example, an admin selects the relevant contact record, applies PI Removal on sensitive fields (names, email, etc.), and confirms the log entries are anonymized [2]. The anonymized record can then be deleted if appropriate (and it will be removed from active UI after 30 days, per NetSuite’s retention policy [45]).
- Export final data set (Portability): If needed, produce a final CSV of the data subject’s remaining data (which would no longer include deleted fields). This satisfies the portability request.
- Document the process: Record in an internal DSAR log that the request was fulfilled, reference the NetSuite actions taken (Saved Search snapshots, time stamps, and user IDs) to demonstrate compliance. NetSuite’s audit trails (System Notes) provide evidence of these actions [41] [18].
NetSuite itself assists administrators in the process. For instance, NetSuite 360 (the admin support portal) includes a Privacy & Compliance request feature [38]. From there, a user with appropriate privileges can subscribe to the Sub-processor list or create compliance requests (the specifics vary by account setup). Although this portal is primarily for Oracle updates (maintenance, subprocessor notices, etc.) [38], it does reflect Oracle’s commitment to transparency. For DSAR handling, NetSuite’s customization capabilities (SuiteScript, saved searches, reporting) are more important.
Several independent analyses note that NetSuite’s built-in controls make it relatively easier to comply with GDPR rights. A Houseblend article states: “NetSuite’s centralized model means…all customer records…are linked to a single customer ID, providing a 360-degree view. This makes it easier to respond to Data Subject Access Requests (DSARs)” [19]. Similarly, Houseblend describes the PI Removal feature as “enabling administrators to scrub or replace personal identifiers…without deleting the entire record. For instance, fields like first name, last name, email, SSN, etc., can be overwritten with generic placeholders… This supports the GDPR ‘right to be forgotten’… by removing sensitive identifiers in the trail [2].” These capabilities correspond exactly to the procedural needs under Articles 15–17 of GDPR.
In summary, NetSuite supplies a toolkit for data subject rights: saved searches, reporting, SuiteAnalytics, export formats for access/portability, editable fields for rectification, and the PI Removal feature for erasure. Controllers must use these tools within defined processes. For example, they may need internal guidelines on how to identify an individual’s data across multiple record types, how to handle nested transactions, and how to use PI Removal judiciously (since it permanently alters data). Training staff on DSAR workflows is essential. But technically, NetSuite does not impose a blocker: the data is accessible and modifiable, and there are mechanisms to comply with each right.
5. Implementation and Best Practices
While NetSuite provides features and contractual safeguards, organizations must implement corresponding internal policies and processes to truly meet GDPR. Some recommended practices include:
-
Data Mapping: Inventory what personal data fields exist in each NetSuite record type. Create “role-specific data dictionaries” so that, for instance, only HR sees payroll IDs and only Sales sees customer contacts. Maintain documentation of where personal data flows into NetSuite (e.g. via web forms, CSV imports, integrations) and where it goes out (reports, BI exports, external suites). This aligns with GDPR’s requirement to document processing activities.
-
Minimal Data Collection: Customize NetSuite forms and fields to collect only needed personal data. Remove or hide unnecessary PII fields from forms (e.g. if SSN is not legally needed for a customer, do not collect it). Use NetSuite’s field-level permissions to ensure users in different roles cannot create or view unneeded personal fields.
-
Consent and Lawful Basis: If processing based on consent (e.g. marketing communications), use custom fields to track the consent date, scope, and source. NetSuite allows adding custom fields to customer/contact records. Record all opt-ins and opt-outs in NetSuite so you can audit your legal basis for marketing or profiling.
-
Sub-processor Management: Regularly review Oracle’s Subprocessors list (available via NetSuite 360) [38]. If your controller organization uses other apps that integrate with NetSuite (e.g. a third-party analytics connector), consider those as additional processors. Ensure those parties also have appropriate DPAs.
-
Privacy by Design Default: Use NetSuite roles and permissions to enforce “privacy by default” – e.g. give access only to data absolutely required for a user’s job. For example, a sales rep should not see employee records; a support agent should not see financial records. Restrict UI and API permissions appropriately.
-
Auditing and Monitoring: Enable and review NetSuite audit trails. The System Notes feature logs all record changes. Periodically run security and compliance audits (NetSuite Security Console or SuiteApp) to detect any misconfiguration. Also, review the Compliance 360 activity log (for Service customers) if enabled [18].
-
Breach Response Plan: Even though NetSuite itself is SOC 2 compliant and Oracle monitors its infrastructure, controllers should have an incident response plan that includes any third-party systems. Understand Oracle’s obligations (e.g. Oracle will notify the controller about breaches affecting NetSuite) and ensure the controller can meet GDPR’s 72-hour breach notification deadline to authorities.
Following these practices, perhaps aided by professional services or compliance consultants, will help align NetSuite use with GDPR demands. The law still considers the controller as ultimately responsible, so ongoing governance (reviews, audits, updates to processes) is critical.
6. Case Examples and Perspectives
While we have focused on the technical and contractual details, it is useful to consider hypothetical use cases to illustrate how GDPR compliance with NetSuite plays out in the real world:
-
Case A – European Subsidiary of a Multinational: A German subsidiary of a US company uses NetSuite to manage sales and finance. The subsidiary decides to have its NetSuite account hosted in Oracle’s EU data centers. It signs the NetSuite DPA (incorporating EU SCCs) and configures field-level permissions so that only German user roles see German customer data. When a German data subject requests all data about them, the subsidiary’s GDPR team runs a Saved Search by email and exports the results, then uses PI Removal on any test records. Here, the combination of EU hosting and DPA with SCC means no unauthorized transfer occurred, and the subsidiary complied with the SAR using built-in tools.
-
Case B – U.S. Company with EU Customers: A U.S.-based e-commerce retailer uses NetSuite (hosted in the U.S.) but collects orders from EU customers. To comply with GDPR, the company relies on Oracle’s DPA which includes EU SCCs [29]. When a EU customer requests data, the company extracts the records via saved searches, redacts as needed, and provides the data in CSV. The data was legally transferred per SCCs, satisfying GDPR Chapter V requirements.
-
Case C – UK Company Post-Brexit: A UK subsidiary uses NetSuite and faces a Brexit situation. Since the UK enjoys an adequacy decision and Oracle’s contracts include a UK Addendum, the NetSuite installation effectively is treated similarly to an EU setup. The UK company can host in London or Dublin and use the existing DPA to meet UK GDPR obligations. Any UK DSAR is processed the same way as an EU DSAR. If a UK citizen exercises data portability, the UK entity can export records as above.
-
Case D – HealthTech Startup (Future Scenario): Consider an EU health tech startup using NetSuite to manage patient billing (non-sensitive finance data). The company might be subject to both GDPR and the new European Health Data Space (EHDS) rules. They ensure patient identifiers are de-identified or treated as special categories. They also review the NetSuite contract for clauses on health data. Although NetSuite is not healthcare-specific, its ISO 27018 implementation and the ability to control access level may help satisfy secondary uses requirements. Future Oracle health-specific offerings (if any) could further align.
These scenarios illustrate that NetSuite’s features (regional hosting, security controls, DPA) and administrators’ actions together enable compliance. No public GDPR enforcement cases specifically involving NetSuite have been announced, but controllers using other cloud services have faced fines when basic obligations were ignored. For example, a French DPA fined an organization €1.7M for inadequate security and lack of breach safeguards [46], underscoring the stakes of Article 32. By contrast, our examples show that using the safeguards NetSuite provides (encryption, code of conduct, DPA, etc.) can significantly mitigate risk, as long as companies also manage the “shared responsibility” side (correct configuration, user training, etc.).
7. Implications and Future Directions
The GDPR framework itself is now well-established, but data protection compliance continues evolving. For NetSuite users, several factors merit attention:
-
Data Localization Trends: Even though GDPR does not mandate strict localization, some industries and laws do (e.g. German health data laws, Indian personal data bill drafts, etc.). Oracle has shown willingness to expand NetSuite regions (e.g. India 2025 [23]) to meet such demands. We may see more localized data center options for NetSuite in countries enacting strict data residency rules.
-
Broadening EU Regulations: New EU initiatives (Data Governance Act, Data Act, Digital Markets Act) emphasize data sharing and portability for non-personal data, or govern platform behaviors. While these do not directly change GDPR, companies using NetSuite must be aware of how these laws might intersect (e.g. a requirement to share IoT or machine data might involve ERP). However, Oracle has begun addressing some: for example, its NetSuite help documentation includes an “EU Data Act” section outlining how to port and delete data [47]. This indicates Oracle’s attention to upcoming mandates.
-
AI and Privacy: As organizations increasingly apply analytics or AI on business data, the privacy stakes grow. NetSuite’s audit trails and consent tracking (via custom fields) will help controllers document lawful AI uses. Oracle and NetSuite may in future add specialized tools for AI governance or personal data discovery. Any generative AI features (e.g. AI-powered insights from ERP data) will need careful handling of personal data to avoid GDPR pitfalls.
-
Regulator Focus: EU Data Protection Authorities (DPAs) continue to scrutinize cloud providers. Oracle’s adherence to the EU Cloud Code of Conduct (with an official approval ID [8]) means it benefits from third-party audits. Nonetheless, DPAs may increase inquiries or audits of major processors. Controllers using NetSuite should keep an eye on relevant DPA guidance (e.g. on SCCs, BCRs, Consent, Data Portability).
-
Cross-Border Politics: Geopolitical changes may influence data transfer rules. The invalidation of Privacy Shield was a story; future developments (like a new EU-US framework or changes to UK adequacy) could arise. Controllers should monitor whether Oracle updates its transfer clauses (and DPAs). As of 2026, Oracle’s DPA references the latest EU SCC sets (2021 rules) and includes clauses for UK/Swiss/Brazil [31] [30], but any major legal shifts will require updates.
-
Technological Updates: NetSuite as a platform keeps evolving (SuiteCloud enhancements, new SuiteApps, etc.). For example, a newer Privacy & Compliance dashboard or SuiteApp might emerge to assist DSARs. Controllers should review Oracle’s release notes (SuiteAnswers) for any new privacy features. Oracle’s broader cloud security portfolio (e.g. CASB, IAM) may be integrated with NetSuite via connectors, offering additional compliance layers.
Finally, we note that while our focus has been GDPR, a global perspective is important. Many countries have adopted GDPR-like laws (UK, Canada’s PIPEDA-modernization – often with SCCs, Brazil’s LGPD which mirrors GDPR, etc.). Organizations running NetSuite internationally will benefit from Oracle’s global DPA frameworks (e.g. Brazilian SCCs). The principle of controllers ensuring rights and processors providing safeguards applies universally.
Conclusion
In conclusion, NetSuite is a mature cloud ERP platform that can support robust GDPR compliance – but only if used correctly. Oracle has laid a strong legal and technical foundation: EU-based data centers and OCI regions allow data residency; a GDPR-aligned DPA (with SCCs and BCRs) addresses transfer rules; and numerous security certifications plus Code-of-Conduct compliance demonstrate “sufficient guarantees” under GDPR Article 28 [8] [6]. The platform also includes specific data-subject rights tools (search/export and PI Removal) that map well onto GDPR requirements [2] [17].
However, there is no one-click solution. Actual compliance depends on the organization’s practices. Controllers must understand GDPR (including national supplements), configure NetSuite to minimize data and tighten access, and establish procedures for consent management, data retention, and DSAR handling. They should execute the requisite legal agreements (Oracle’s DPA and any addenda) and verify sub-processors. In effect, NetSuite’s compliance readiness makes it machine-ready, but humans must drive the process correctly. Without proper governance, even the best-designed system can fail to meet GDPR’s “lawfulness, fairness and accountability” standards [10].
For IT and privacy officers evaluating NetSuite, the evidence is reassuring that Oracle has done its part: adoption of global privacy covenants, continuous monitoring of cloud infrastructure (ISO/SOC audits), and transparent policies. Independent experts have also affirmed that “NetSuite is GDPR-compliant, yes, with conditions” [48] [49] – meaning the conditions are satisfied when customers follow best practices.
Looking ahead, NetSuite users should watch for emerging EU rules (such as new data portability mandates) and for Oracle’s platform enhancements in privacy. The broader trend of data localization and sovereignty suggests that Oracle will continue expanding its regional cloud offerings, further easing residency concerns. Meanwhile, global privacy convergence (via adequacy efforts or international codes) will simplify cross-border NetSuite usage over time.
In summary: Oracle NetSuite provides the necessary technical controls and contractual assurances to meet GDPR obligations – but it is ultimately a “shared responsibility model”. Organizations using NetSuite must actively configure and operate the system in compliance with GDPR principles. When they do, NetSuite can indeed be a GDPR-compliant data management solution.
Sources: Our findings above are based on Oracle/NetSuite documentation and technical white papers [3] [17], GDPR legal texts and guidance (Source: gdpr-info.eu) [16], and analyses by industry and legal experts [6] [49]. All statements have been supported with citations to these credible sources.
External Sources
About Houseblend
HouseBlend.io is a specialist NetSuite™ consultancy built for organizations that want ERP and integration projects to accelerate growth—not slow it down. Founded in Montréal in 2019, the firm has become a trusted partner for venture-backed scale-ups and global mid-market enterprises that rely on mission-critical data flows across commerce, finance and operations. HouseBlend’s mandate is simple: blend proven business process design with deep technical execution so that clients unlock the full potential of NetSuite while maintaining the agility that first made them successful.
Much of that momentum comes from founder and Managing Partner Nicolas Bean, a former Olympic-level athlete and 15-year NetSuite veteran. Bean holds a bachelor’s degree in Industrial Engineering from École Polytechnique de Montréal and is triple-certified as a NetSuite ERP Consultant, Administrator and SuiteAnalytics User. His résumé includes four end-to-end corporate turnarounds—two of them M&A exits—giving him a rare ability to translate boardroom strategy into line-of-business realities. Clients frequently cite his direct, “coach-style” leadership for keeping programs on time, on budget and firmly aligned to ROI.
End-to-end NetSuite delivery. HouseBlend’s core practice covers the full ERP life-cycle: readiness assessments, Solution Design Documents, agile implementation sprints, remediation of legacy customisations, data migration, user training and post-go-live hyper-care. Integration work is conducted by in-house developers certified on SuiteScript, SuiteTalk and RESTlets, ensuring that Shopify, Amazon, Salesforce, HubSpot and more than 100 other SaaS endpoints exchange data with NetSuite in real time. The goal is a single source of truth that collapses manual reconciliation and unlocks enterprise-wide analytics.
Managed Application Services (MAS). Once live, clients can outsource day-to-day NetSuite and Celigo® administration to HouseBlend’s MAS pod. The service delivers proactive monitoring, release-cycle regression testing, dashboard and report tuning, and 24 × 5 functional support—at a predictable monthly rate. By combining fractional architects with on-demand developers, MAS gives CFOs a scalable alternative to hiring an internal team, while guaranteeing that new NetSuite features (e.g., OAuth 2.0, AI-driven insights) are adopted securely and on schedule.
Vertical focus on digital-first brands. Although HouseBlend is platform-agnostic, the firm has carved out a reputation among e-commerce operators who run omnichannel storefronts on Shopify, BigCommerce or Amazon FBA. For these clients, the team frequently layers Celigo’s iPaaS connectors onto NetSuite to automate fulfilment, 3PL inventory sync and revenue recognition—removing the swivel-chair work that throttles scale. An in-house R&D group also publishes “blend recipes” via the company blog, sharing optimisation playbooks and KPIs that cut time-to-value for repeatable use-cases.
Methodology and culture. Projects follow a “many touch-points, zero surprises” cadence: weekly executive stand-ups, sprint demos every ten business days, and a living RAID log that keeps risk, assumptions, issues and dependencies transparent to all stakeholders. Internally, consultants pursue ongoing certification tracks and pair with senior architects in a deliberate mentorship model that sustains institutional knowledge. The result is a delivery organisation that can flex from tactical quick-wins to multi-year transformation roadmaps without compromising quality.
Why it matters. In a market where ERP initiatives have historically been synonymous with cost overruns, HouseBlend is reframing NetSuite as a growth asset. Whether preparing a VC-backed retailer for its next funding round or rationalising processes after acquisition, the firm delivers the technical depth, operational discipline and business empathy required to make complex integrations invisible—and powerful—for the people who depend on them every day.
DISCLAIMER
This document is provided for informational purposes only. No representations or warranties are made regarding the accuracy, completeness, or reliability of its contents. Any use of this information is at your own risk. Houseblend shall not be liable for any damages arising from the use of this document. This content may include material generated with assistance from artificial intelligence tools, which may contain errors or inaccuracies. Readers should verify critical information independently. All product names, trademarks, and registered trademarks mentioned are property of their respective owners and are used for identification purposes only. Use of these names does not imply endorsement. This document does not constitute professional or legal advice. For specific guidance related to your needs, please consult qualified professionals.