NetSuite Single Sign-On: SAML 2.0 & OIDC Setup Guide
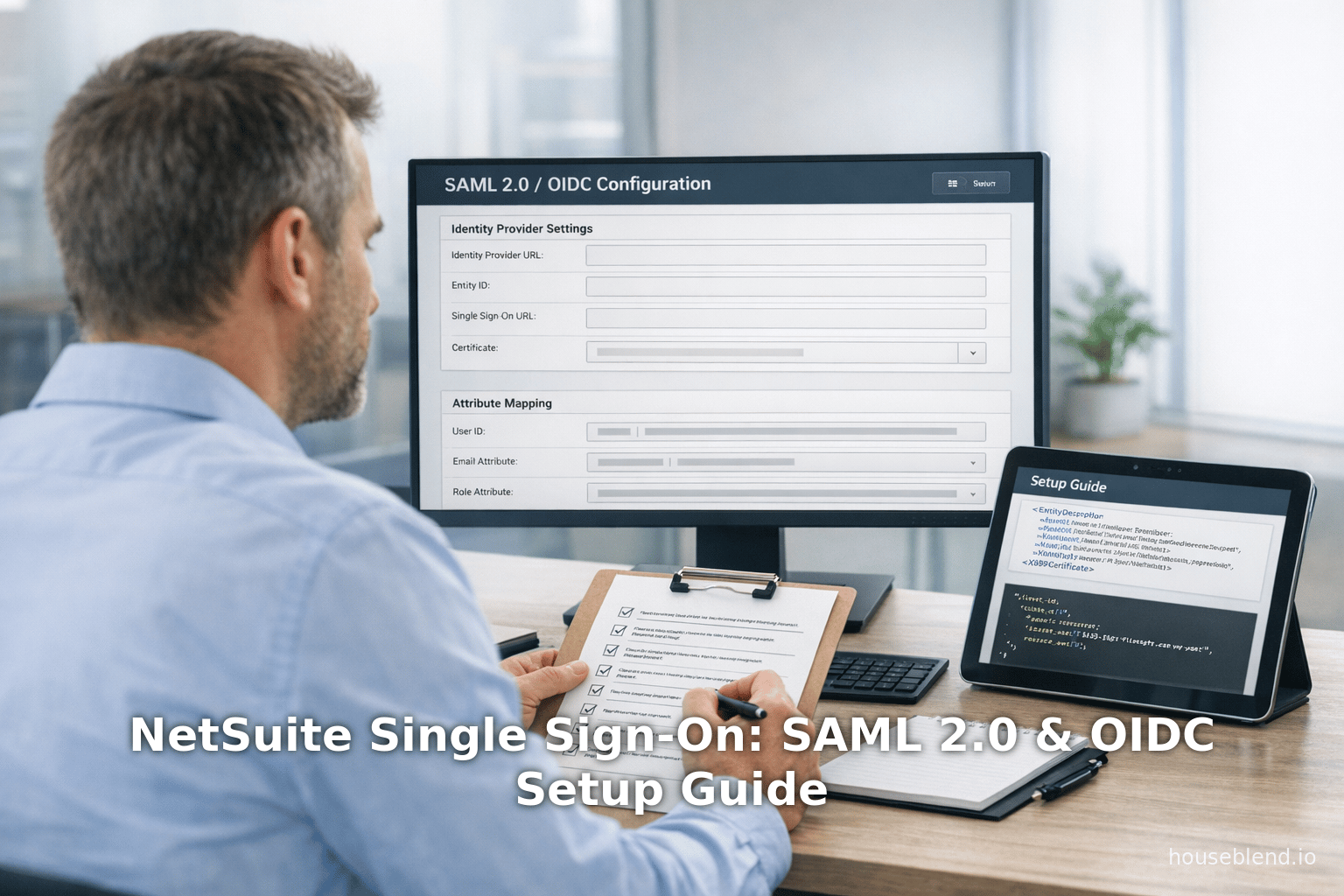
NetSuite Single Sign-On Configuration: SAML 2.0, OIDC and Identity Provider Setup Guide
Executive Summary: NetSuite—a leading cloud-based ERP/CRM—supports federated Single Sign-On (SSO) through industry-standard protocols SAML 2.0 and OpenID Connect (OIDC). This report provides an in-depth, evidence-backed guide to configuring both SAML and OIDC SSO for NetSuite, including technical steps, comparisons of protocols, identity provider (IdP) integration procedures, and real-world examples. We draw on official NetSuite and Oracle documentation, identity-platform white papers, and industry analysis to paint a comprehensive picture. Key findings include:
-
NetSuite SAML SSO: Administrators enable the SuiteCloud SSO feature and configure NetSuite as a SAML Service Provider (SP). They provide NetSuite’s SP metadata (entity ID, ACS URL, SLO endpoint) to the IdP and enter the IdP’s metadata (issuer, SSO URL, certificate) into NetSuite [1] [2]. Popular IdPs (Okta, Azure AD, Google Workspace, OneLogin, Ping, etc.) each have guides or built-in apps for NetSuite integration [3] [4]. Common pitfalls include certificate format (NetSuite requires Base64 X.509) [5] and mismatched account IDs [6]. Proper attribute mapping is critical; for example, NetSuite expects attributes like
emailandaccountto identify users [7] [4]. -
NetSuite OIDC SSO: An alternative to SAML, NetSuite’s OIDC feature lets an external OIDC Provider (OP) handle authentication. Administrators must enable the OIDC SSO feature and register NetSuite as an OIDC relying party (RP). Configuration involves entering the Client ID/secret and endpoints (or a discovery URL) from the OP into NetSuite [8] [9]. Users can initiate OIDC sign-on via a special NetSuite login URL (e.g.
https://<account>.app.netsuite.com/app/login/secure/oidc.nl) [10]. Any certified OIDC provider (e.g. Okta, Azure AD / Microsoft Entra ID, Auth0) can serve as OP. A security warning is raised when enabling OIDC SSO: the administrator must accept that third-party IdPs can now directly access NetSuite, and ensure compliance with standards (PCI, etc.) [11] [12]. -
Protocol Comparison: SAML 2.0 (introduced ~2005 [13]) is XML-based and widely adopted in enterprises, carrying rich signed assertions with granular attributes [14]. OIDC (standardized ~2014) uses JSON Web Tokens (JWT) atop OAuth2 [15], favoring modern web/mobile use cases. Both can secure NetSuite SSO, but SAML remains pervasive in existing deployments [16], while OIDC offers lighter-weight JSON flows. The protocols have different strengths and idiosyncrasies (see Table 1).
-
Identity Providers: Major IdPs provide pre-built NetSuite integrations. For example, Okta’s application catalog includes a NetSuite SAML connector, requiring entry of the ACS URL and partial attribute mapping [3] [7]. Azure AD’s gallery app automates many fields [17]. Google Workspace supplies a “NetSuite (SAML)” app with guided field setup (mapping Google’s Primary Email to NetSuite’s
email, and NetSuite’s account ID to theaccountattribute) [4]. Ping Identity and OneLogin similarly offer connectors or wizards [18]. NetSuite provides general instructions to create a new SP app in the IdP, upload or paste NetSuite’s SP metadata, and supply the IdP’s metadata back into NetSuite [19] [1]. -
Data & Trends: Enterprise SSO is now a standard requirement: an industry survey found 81% of organizations (>$5M ARR) support enterprise SSO, up from 67% in 2024 [20]. Recent analyses note that SAML’s rich assertion model suits legacy systems while OIDC’s simpler JSON tokens appeal to modern developers [21] [14]. A U.S. cybersecurity study highlights that SMBs face barriers to SSO adoption, implying extra effort may be needed to implement SAML/OIDC securely [22]. Oracle’s own guidance on NetSuite SSO warns about feature-enablement risks, emphasizing that allowing external IdPs changes the security model [11].
-
Case Examples: Oracle documentation for NetSuite Analytics Warehouse notes SAML SSO with Azure AD/Okta and OIDC SSO with Azure AD, Okta, or even NetSuite itself [23], illustrating real-world use. In “SuiteCommerce” ( NetSuite e-commerce scenarios, integrators have built custom flows where NetSuite acts as the Identity Provider for customers, enabling unified login across portals [24] [25]. These examples show the flexibility of NetSuite-based SSO solutions.
-
Future Directions: NetSuite will likely continue supporting both SAML and OIDC; enterprises trend toward OIDC for new applications but SAML’s enterprise install base endures [21] [14]. Enhanced security (MFA, risk-based auth, passwordless/FIDO) can be layered on top of SSO. Organizations should monitor emerging standards (like SCIM for provisioning) and evolving security policies.As identity federation grows ubiquitous [20], NetSuite’s SSO capabilities will remain fundamental to secure, user-friendly access.
The following sections cover background context, technical details, implementation steps, and analyses for each topic above, with extensive citations and examples.
Introduction
Enterprise SSO and NetSuite. In modern enterprises, Single Sign-On (SSO) allows users to authenticate once and access multiple applications without re-entering credentials. Key benefits include reduced password fatigue, fewer help-desk tickets, and stronger security through a centralized authentication policy. NetSuite—a cloud-based ERP and CRM platform widely used by mid-market and large organizations—supports enterprise SSO to integrate seamlessly into corporate identity infrastructures. As Oracle’s documentation explains, NetSuite can rely on external identity providers (IdPs) like Microsoft Entra (Azure AD), Okta, Google, Ping, and others for federated login [26] [1].
SSO in NetSuite is achieved via two main protocols: SAML 2.0 and OpenID Connect (OIDC). SAML 2.0 (Security Assertion Markup Language) is an XML-based standard developed by OASIS, finalized around 2005 [13]. It has long been the de facto enterprise SSO method, supported by legacy identity systems (e.g. ADFS, Shibboleth, PingFederate) and many SaaS apps [27] [16]. OIDC is a newer standard (2014) that builds an identity layer on OAuth 2.0, using JSON Web Tokens (JWT). It addresses modern needs (mobile, APIs, social login) and is simpler for developers [15] [21]. NetSuite’s OIDC SSO feature was added more recently to give administrators a choice beyond SAML [28].
Scope of this report. This report delivers a comprehensive, step-by-step guide to configuring NetSuite SSO with SAML 2.0 and OIDC. It includes:
- Background on SAML vs. OIDC (their architectures, data formats, use cases – see Table 1 below).
- How to enable SSO features in NetSuite and set up the NetSuite SAML/OIDC configuration pages.
- Detailed IdP setup instructions for major providers (Okta, Microsoft Entra/Azure AD, Google Workspace, OneLogin, etc.) with required metadata and attribute mappings.
- Examples and best practices (e.g. attribute requirements, certificate handling, default URLs).
- Discussion of security considerations, and future trends in identity federation.
All factual statements are supported by official documentation or expert sources, cited inline. Where possible, we include real-world scenarios or vendor case examples to ground the discussion.
SAML 2.0 Single Sign-On with NetSuite
SAML 2.0 Overview
Security Assertion Markup Language (SAML) 2.0 is an XML-based protocol for exchanging authentication and authorization data between parties – typically an IdP and a Service Provider (SP). In a NetSuite context, NetSuite acts as the SAML SP and delegates authentication to an external IdP. The IdP (e.g. Okta, Azure AD, Google) authenticates the user and issues a signed SAML Assertion containing attributes (like username, roles, email) to NetSuite. NetSuite then logs the user in with the appropriate permissions. This allows corporate credentials (for example, Active Directory accounts) to control access to NetSuite without separate NetSuite passwords.
Why SAML 2.0? SAML’s structured assertions are particularly suited to enterprise use-cases that require rich claims and complex role/attribute semantics. As one industry analysis observes, “SAML Assertions: Digitally signed XML documents that carry rich, hierarchical identity information… well-suited for complex enterprise needs like role-based access control” [14]. SAML is deeply entrenched: major IdPs (ADFS, Ping, Okta, Shibboleth) and thousands of SaaS apps use it [16]. NetSuite has supported SAML SSO for many years, making it the standard integration for large IT organizations.
Table 1 (below) contrasts SAML 2.0 and OIDC on various dimensions. Notable points:
- Data format: SAML uses XML assertions, whereas OIDC uses JSON and JWT [15] [14].
- Complexity vs modernity: SAML messages are verbose but highly structured (with standard statements like
<saml:AuthnStatement>and<saml:AttributeStatement>[14]). OIDC’s JSON Web Token is lighter and more web/dev-friendly. - Adoption: SAML still “dominates enterprise authentication” due to legacy investments [29] [16], even as OIDC gains ground.
Table 1. Protocol Comparison: SAML 2.0 vs. OpenID Connect (OIDC)
| Aspect | SAML 2.0 | OpenID Connect (OIDC) |
|---|---|---|
| Introduced | 2002 (OASIS standard) [13] | 2014 (built on OAuth 2.0) |
| Data format | XML (SAML Assertions) [14] | JSON Web Tokens (JWT) and JSON payloads [15] |
| Protocol base | Security-focused XML protocol | OAuth 2.0 with identity layer |
| Common Use-cases | Enterprise SSO, federated SSO for web portals | Modern web/mobile apps, APIs, SaaS logins |
| Trust Setup | Requires exchanging metadata (certs, URLs) | Uses JSON endpoints and client credentials |
| Token Semantics | Rich, typed AttributeStatements (roles, etc.) [14] | JWT with standard claims (sub, email, etc.) |
| IdP vs SP Roles | Clearly defined IdP (sends SAML) and SP | OP (Authorization Server) issues ID tokens |
| Binding/Flow | Browser redirect with signed XML payloads; supports POST, Redirect bindings | OAuth2 flows (authorization code, implicit) with JSON responses |
| Adoption & Networks | Extensive enterprise support, network effect [16] | Rapidly growing (consumer and enterprise) |
| Examples | Used by Okta, Azure AD (SAML app), Google (SAML app) for NetSuite [3] [4] | Supported by any OIDC-compliant IdP (Okta OIDC, Azure AD’s OAuth, etc.) |
Enabling SAML SSO in NetSuite
Before configuring SAML, an administrator must enable the SAML SSO feature in NetSuite. In NetSuite, go to Setup > Company > Enable Features > SuiteCloud subtab. Under Manage Authentication, check SAML Single Sign-on, accept the terms, and save [30]. (If the menu option isn’t visible, the admin role may need the “Enable Features” permission.) A warning is displayed: by enabling SAML SSO, users can log in via a third-party IdP, so security practices must assume the IdP now controls authentication [31].
After enabling, the SAML Setup page becomes available: Setup > Integration > SAML Single Sign-on [32]. This page (accessible only to admins or users with the Set Up SAML SSO permission) is where the SP and IdP settings are entered. Key fields include:
- Identity Provider (IdP) Entity/Issuer: The issuer URI from the IdP metadata (e.g. Okta’s entity or Azure AD’s tenant URI) [2].
- Identity Provider Login URL: The SAML SSO endpoint where NetSuite should redirect for login (the IdP’s SSO login page URL).
- Identity Provider Certificate: The X.509 signing certificate from the IdP, uploaded or pasted. NetSuite will use this to verify SAML signatures [2].
- Entity ID / Service Provider Issuer: NetSuite’s own entity ID (by default
https://<account>.app.netsuite.com/saml2/acs) [33]. This must match the ACS (Assertion Consumer Service) URL seen by the IdP. - Logout Landing Page (optional): A URL to redirect users when they logout.
- Primary Authentication Method (optional): You can choose whether to force SAML as primary login or allow NetSuite passwords as fallback.
Administrators also define a Logout Landing Page, which is where users go when they fully log out (if Single Logout is used, the IdP’s logout might redirect there) [34]. These fields align with the NetSuite SP metadata file, which you can download from this setup page. The SP metadata (an XML document) contains crucial values (SP entityID, AssertionConsumerService URL, SLO URL, etc.) that are given to the IdP [19] [1].
NetSuite SP Metadata: Instead of manual entry, you typically give the IdP NetSuite’s SP metadata. Either upload the metadata file or provide a metadata URL. The table below (from Oracle docs) shows how NetSuite SP metadata fields map to what the IdP needs:
| NetSuite SP Metadata Field | Description / Value [1] [35] |
|---|---|
| SP Entity ID | The entityID in the NetSuite metadata (first line of XML). This is typically https://<account>.app.netsuite.com/saml2/acs for the account. Copy this into the IdP’s “Audience” or “Entity ID” field. |
| Assertion Consumer Service | The URL where SAML Responses should be sent (ACS URL). By default it is https://system.netsuite.com/saml2/acs. Oracle notes you do not need to change it if NetSuite’s data center moves [36]. |
| Single Logout Service (SLO) | The URL for logout (NetSuite will post to this on global logout). Use the POST binding at https://system.netsuite.com/saml2/slopost (only the first URL in the metadata list) [35]. |
After entering the IdP fields and uploading the IdP certificate, you save the NetSuite SAML Setup page. NetSuite then shows an SP metadata URL (a Public URL). This can be given to the IdP if needed; it essentially points to the same data as the SP metadata file [33].
Identity Provider Configuration (SAML)
On the IdP side (e.g. Okta, Azure AD, etc.), you must create a SAML application and configure it for NetSuite. The exact steps vary by platform, but the general process is: (1) Add a new SP application (often called “NetSuite” or a “Custom SAML App”), (2) import or enter NetSuite’s SP metadata (or fill ACS/Entity etc. manually), (3) set Issuer/Entity (from metadata or as recommended by NetSuite), and (4) specify NameID format and attribute mappings.
Okta Example: Okta provides an “Oracle NetSuite” application with preconfigured defaults. To configure Okta SSO for NetSuite:
-
In Okta Admin, Add Application > Browse App Catalog, search for “NetSuite” and choose the Oracle NetSuite SAML app [37].
-
When adding, Okta prompts for the NetSuite account ID (e.g.
1234567) [38]. Okta then creates the app. -
Under the Sign On tab, choose SAML 2.0. Set key values:
-
Okta will generate SSO metadata: download the IdP metadata XML or at least note the SSO URL/Issuer and certificate for NetSuite.
-
Attribute Statements (mapping): Okta must include at least two attributes:
email→ user's email (NetSuite uses this as the primary login ID).account→ static string equal to your NetSuite account ID (e.g."1234567"). Optional:role→ an internal NetSuite Role internal ID to auto-assign a role on login. (If omitted, the user goes to their default role.) [7]. In Okta’s app settings, mapuser.emailto theemailattribute and create a custom attributeaccountset to your NetSuite ID. .
-
Assign Users/Groups: In Okta, assign the NetSuite app to the users or group of users who should have SSO (under Assignments in Okta). Only assigned users can SSO to NetSuite [39].
Once Okta is configured, copy the Okta IdP Issuer URL and SSO URL (from Okta’s metadata) and import into NetSuite (as described above). After that, users in Okta can sign into NetSuite via Okta SSO (e.g. using the Okta dashboard or the NetSuite SSO URL).
Azure AD Example: Microsoft Entra ID (Azure AD) also offers a built-in Oracle NetSuite app.
- In Azure portal, go to Azure AD > Enterprise Applications > New Application. Search for “NetSuite” and select Oracle NetSuite, then Create.
- In the NetSuite app, go to Single Sign-On > SAML. For Basic SAML Configuration, set:
- Identifier (Entity ID):
https://<accountId>.app.netsuite.com/saml2/acs. - Reply URL (ACS URL): same as the ACS above.
- Sign-on URL:
https://<accountId>.app.netsuite.com/app/login/secure/sso.nl(Azure uses this as a landing page). - Logout URL:
https://<accountId>.app.netsuite.com/saml2/slo. (It’s important the ACS/Entity values match those expected by NetSuite) [40].
- Identifier (Entity ID):
- In Attributes & Claims, configure:
- Name Identifier (Name ID):
user.userprincipalnameoruser.mailin email format [41]. - Custom Claims: an
accountclaim set to a constant value of your NetSuite account ID. - Optionally a
roleclaim from a user attribute or group claim for role provisioning.
- Name Identifier (Name ID):
- Certificates & Metadata: Download the Azure AD SAML Signing Certificate (Base64) and the Federation Metadata XML [42].
- User Assignment: Assign Azure AD user/groups to the NetSuite application (Azure will only allow assigned users to SSO).
Then, copy the Azure AD Login URL (SSO URL), Azure AD Identifier (issuer), and the downloaded certificate, and paste/upload them into NetSuite’s Identity Provider fields as above [2]. Finally, in NetSuite assign the SSO permission to roles of those users.
Both Okta and Azure support the necessary workflow with minimal custom steps (Okta via its catalog app, Azure via Gallery). In contrast, some IdPs (e.g. ADFS or a custom SAML) require manual configuration by copying values. Oracle’s documentation provides general guidance: “you must provide the NetSuite Service Provider Metadata to your IdP” either by uploading NetSuite’s metadata file or pasting its URL [19], and then copying required fields (Entity ID, ACS, SLO) from the metadata into the IdP [1]. After that, one must “download the IdP metadata file or copy the IdP metadata URL” to import back into NetSuite [43].
Oracle cautions that the format and exact values must match: for example, the ACS URL defaults to the system domain (system.netsuite.com) and usually does not change [36] even if the account moves data centers. Also, NetSuite expects the certificate in Base64-encoded X.509 format [5]; uploading a DER-encoded cert will silently fail.
Essential SAML Configuration Details
A few critical details and best practices emerge from the documentation and expert guides:
- NameID / Identifier: NetSuite by default uses the
emailaddress as the principal identifier. The IdP must send the user’s email (or a unique NetSuite login) in the SAMLNameIDor an attribute. Okta and Azure examples set NameID = user.email [3] [41]. - Account ID (Organization ID): NetSuite’s account ID (numeric or alphanumeric) must be passed as an attribute named
account[7] [4]. This ensures the assertion is applied to the correct NetSuite account. This attribute is typically a constant in the IdP configuration. - Role Provisioning: Optionally, include a
roleattribute (the internal ID of a NetSuite Role), so the IdP can control which Role the user assumes. If omitted, NetSuite logs the user into their default role [44]. - User Records in NetSuite: Each IdP user must correspond to a NetSuite user record (employee, customer, or partner). This means after SSO login, NetSuite matches the incoming email to a user. The SSO does not auto-create users unless provisioning is set up separately. Ensure each relevant user exists in NetSuite with the correct email and role assignments.
- Role Permissions: The NetSuite role(s) that users may assume via SSO must have the “Set Up SAML Single Sign-on” permission if they need to configure SSO. In practice, designate a specific admin role for SSO setup [32]. Also, users must have the proper role permissions to access NetSuite normally.
- Single Logout (SLO): If you wish to enable logout from IdP, note the SLO endpoint. NetSuite provides an SLO URL (
/saml2/slopost) which the IdP can call to trigger a NetSuite logout. IdPs often optionally configure a logout URL pointing to NetSuite. Use POST binding for SLO [35]; some IdPs may support it out of the box. - Certificate Renewal: NetSuite requires an X.509 certificate to verify the IdP’s SAML assertions. When an IdP’s certificate is renewed, you must upload the new certificate on the NetSuite side. Be aware NetSuite does not send an error if the certificate is wrong [5]; SSO will simply silently fail on login.
- Testing and Troubleshooting: Always test SSO with a test user or role first. Common issues include certificate format mismatches, typos in the SP/IdP URLs, or forgetting to assign users to the IdP application. Use browser tools or SAML-tracer plugins to inspect the outgoing SAML assertion for debugging.
Table: Common NetSuite Identity Providers
Below is a summary of popular IdPs and their NetSuite support. All listed providers support SAML; many also support OIDC with NetSuite’s OIDC feature.
| Identity Provider | SAML Support | OIDC Support | NetSuite Integration Notes |
|---|---|---|---|
| Okta | Yes (Pre-built app) [3] | Yes (OIDC app) | Okta has a NetSuite SAML app in the catalog. Enter NetSuite ACS as above. Map user.email to email, and set account attribute. Okta also offers OIDC apps for id_token login. |
| Microsoft Entra (Azure AD) | Yes (Gallery Oracle NetSuite app) [45] | Yes (via Azure OAuth/OIDC endpoints) | Azure’s built-in Enterprise App allows easy SAML setup. For OIDC, one can use Azure App registrations (OIDC) or Azure AD B2C, supplying its endpoints to NetSuite. |
| Google Workspace (GSuite) | Yes (Google SAML “NetSuite” app) [4] | No (Google IdP does not provide generic OIDC for non-Google apps) | Google Admin provides a NetSuite SAML template. It maps Google Email → NetSuite email, and a custom “NetSuite Account ID” field → NetSuite account [4]. |
| OneLogin | Yes (App connector) [18] | Yes (OIDC app) | OneLogin has a prebuilt NetSuite connector with SAML support [18]. Configuration is similar (upload NetSuite metadata, assign users). |
| Ping Identity | Yes (SAML) | Yes (OIDC) | PingFederate or PingOne can integrate via standard SAML SSO. Known for enterprise use. |
| ADFS / Azure AD FS | Yes (SAML) | In newer versions (via OAuth/OIDC) | Microsoft's on-prem AD FS can be configured as NetSuite IdP by manually entering metadata. |
| Auth0 / Okta OIDC | N/A (Auth0 is OIDC) | Yes (OIDC) | Identity-as-a-Service like Auth0 can act as OIDC provider. Configure NetSuite RP on the Auth0 side (client ID/secret, redirect URI as NetSuite OIDC URL). |
| Twitter / Others | N/A | (OIDC not relevant) | Many consumer IdPs (Facebook, Google, etc.) are not applicable for enterprise SSO login. |
| NetSuite itself | N/A | Yes (as OIDC provider) | Newer feature: one NetSuite account can serve OIDC to another (for SuiteCommerce or cross-account SSO) [23]. |
OpenID Connect (OIDC) Single Sign-On with NetSuite
OIDC Overview
OpenID Connect (OIDC) is an identity layer built on OAuth 2.0. In OIDC, an external OpenID Provider (OP) (such as Okta, Azure AD, Google Identity, etc.) issues an ID Token via OAuth flows, asserting the user’s identity. NetSuite can be configured as an OIDC Relying Party (RP), meaning NetSuite trusts an OP to authenticate users.
Key differences from SAML:
- OIDC uses JSON/JWT instead of XML [15].
- Authentication typically uses an OAuth redirect (authorization code flow).
- It is often seen as more developer-friendly and mobile-oriented.
NetSuite introduced an OIDC SSO feature to complement SAML [28]. Oracle notes that “OIDC adds an identity layer on top of OAuth 2.0” and users can switch between OIDC SSO roles across accounts [28]. The OIDC provider manages user credentials, and NetSuite is simply the client (RP) [28].
Enabling OIDC SSO in NetSuite
To use OIDC SSO, first enable the feature in NetSuite: Setup > Company > Enable Features > SuiteCloud tab, and check OpenID Connect (OIDC) Single Sign-on [12]. As with SAML, a warning is shown: enabling OIDC SSO allows third-party identity providers to log directly into NetSuite, so security/compliance teams must ensure this meets requirements (e.g. PCI-DSS, MFA policies) [11].
Once enabled, go to Setup > Integration > Manage Authentication > OpenID Connect (OIDC) Single Sign-on [46]. On this NetSuite page, you configure the OIDC connection by filling in settings obtained from your OIDC provider. The main fields are:
- Client ID: The OIDC client identifier that your OP issued when you registered NetSuite as an application (or app) on the OP side [47] [8].
- Client Secret: The client secret (if applicable) from the OP registration [8].
- Post Logout Redirect URL (optional): If your OP supports RP-initiated logout, this is where users return after logging out. Must match the OP’s registered logout URI [48].
- Allowed Email Domains (optional): A whitelist of email domains. NetSuite will only allow OIDC logins for users whose email belongs to one of these domains. If left blank, any domain is allowed [49].
- Set Configuration From URL: A checkbox (defaulted on) where you enter the “configuration URL” or “discovery URL” from your OP(often an URL ending in
/.well-known/openid-configuration) [50] [51]. This lets NetSuite auto-fill issuer, authorization endpoint, token endpoint, and JWKS URI.- If you uncheck this (manual mode), you must input each endpoint manually: Issuer, Authorization Endpoint, Token Endpoint, and Certificate (JWKS) URL, as well as End Session Endpoint for logout if desired [9].
- Submit and save. NetSuite will test the configuration and confirm success.
After saving, NetSuite will display a confirmation. Users can now log in via OIDC.
Using OIDC SSO
When OIDC SSO is configured, users may access NetSuite in two main ways (Oracle documentation):
- Initiate from the OP portal: The user logs into the OP’s dashboard (e.g. Okta or Azure portal) and clicks the NetSuite application link. This sends the user to NetSuite via OIDC.
- Direct OIDC login URL: The user navigates to the NetSuite OIDC endpoint. NetSuite provides these special login URLs:
https://<account>.app.netsuite.com/app/login/secure/oidc.nl- (For Customer Center roles)
https://<account>.app.netsuite.com/app/login/secure/oidcprivate.nlWhen the user visits these, NetSuite will redirect them to the OP’s authorization endpoint (login page). After the user authenticates there, the OP returns them to NetSuite with an OIDC ID token, logging them in [52].
Internally, NetSuite uses the standard OAuth2 code flow: NetSuite (the RP) receives an authorization code from the OP, exchanges it for an ID Token (JWT) and access token, and then validates the ID Token signature against the OP’s published keys [15]. The ID Token contains claims such as sub (subject), email, and any custom ones defined. NetSuite will likely match the email claim to a NetSuite user (similar to SAML’s email mapping) to establish the session.
OIDC Provider Configuration
To allow NetSuite as an RP, you must first configure the NetSuite application on the Identity Provider side:
-
Register a New App (RP) on the OP: In your identity provider (for example, Okta, Azure AD, or any other OIDC-compliant IdP), create a new OIDC application or “Client”.
- Give it a name (e.g. “NetSuite”) and configure it for OIDC/OAuth flow.
- In the settings, set the Redirect URI(s) to NetSuite’s OIDC endpoints (e.g.
https://<account>.app.netsuite.com/app/login/secure/oidc.nlandoidcprivate.nl). - Note the Client ID and Client Secret that the OP issues.
-
Discovery / Endpoints: The OP will have a discovery URL (often ending in
/.well-known/openid-configuration) or static endpoints for:- Issuer URL
- Authorization endpoint (login page)
- Token endpoint (for code exchange)
- JWKS URI (for public keys, or sometimes a Certificate URL)
- End Session endpoint (if supporting post-logout redirection).
-
Configure Claims/Scopes (optional): By default, OIDC ID Token at least includes
sub,email, possiblygiven_name/family_name. Ensureemailis in the token. Some providers let you customize claim mappings (for example, add agroupsclaim if you want group info).
After setting up the OP and obtaining the above details, you return to NetSuite’s OIDC Setup page and enter them:
- Input the Client ID and Client Secret provided by the OP [8].
- Optionally the Post Logout URL if using logout.
- Under Configuration From URL, paste the OP’s discovery URL [51]. NetSuite will fill in the rest automatically. Alternatively switch to manual and paste each endpoint URL and the certificate (JWKS) URL [9].
- Enter any Allowed Email Domains (e.g.
example.com) to restrict logins to your organization’s email domain [49].
NetSuite also asks for “OP domain” (issuer). If using the discovery URL, NetSuite can retrieve this itself; otherwise manually fill it with the issuer from the OP (e.g. https://dev-12345.okta.com or Azure’s https://login.microsoftonline.com/{tenantId}/v2.0).
Once the configuration is saved, NetSuite will show a success message. End-users can now attempt OIDC login: NetSuite will redirect them to the OP’s sign-on page, they authenticate with the OP, and then are redirected back logged-in.
Example OIDC Providers: Popular providers that can serve as OIDC OP for NetSuite include:
- Okta OIDC: Okta supports OIDC (OAuth 2). You would create a new Okta “OIDC” app (OpenID Connect app) and use its credentials in NetSuite.
- Azure AD (Microsoft Entra): You can register a new Azure AD App (App registration) and expose OIDC endpoints. Azure issues a client ID/secret and metadata URL.
- Auth0, PingOne, Keycloak, AWS Cognito, Google Identity (Google Cloud Identity): All support OIDC. In each, register NetSuite as an application, get credentials/URLs, and plug into NetSuite.
- NetSuite as OP: Oracle also allows one NetSuite account to serve as an OIDC Provider for another (as seen in Analytics Warehouse integration [23]), but this is more advanced (see Oracle’s “NetSuite as OIDC Provider” docs).
Security Considerations: Enabling OIDC SSO means trusting the OP fully. Oracle’s documentation warns administrators: “By enabling the OIDC SSO feature, you allow users to access and use your NetSuite account directly from a third-party service that may not have the same authentication and security features as NetSuite” [11]. This emphasizes ensuring the OP’s security (MFA, secure JWT handling) is strong. NetSuite writes, “The identity management system gains administration over user access” [11], so organizations must confirm regulatory compliance (e.g. PCI) when allowing OIDC login.
Table: SAML vs OIDC Comparison (Summary)
| Feature/Aspect | SAML 2.0 (NetSuite) | OIDC (NetSuite) |
|---|---|---|
| Role in SSO | NetSuite is SAML SP (relies on IdP). | NetSuite is OIDC RP (relying party). |
| Data Format | SAML Assertions (XML) [14]. | ID Token (JWT, JSON) [15]. |
| Transport | HTTP Redirect/POST with XML payload. | OAuth2 redirect (authorization code flow) with JSON tokens. |
| Identity Assertion | “Assertion” carrying username, attributes. | JWT carrying claims (sub, email, etc.). |
| Metadata Exchange | Requires exchanging and importing SP/IdP metadata files/URLs [19] [1]. | Mostly endpoint URLs/discovery (JSON). |
| Attribute Flexibility | Rich attribute statements (SAML attributes are hierarchical) [14]. | Predefined claims (standard OIDC claims) but extensible via custom claims. |
| Common IdP Examples | Okta (SAML App), Azure AD (SAML), Google Workspace. | Okta (OIDC App), Azure AD (App registration), Auth0, etc. |
| NetSuite Setup | Enable SAML SSO feature, configure SAML Setup page. | Enable OIDC SSO feature, configure OIDC page. |
| Migration Note | SAML is well-established in enterprises [16]; often legacy SSO. | OIDC is newer, favored in modern apps development. |
Integrating Common Identity Providers
This section gives concrete implementation notes and tips for popular IdPs when setting up NetSuite SSO. For each, official docs and community guides provide step-by-step instructions.
Google Workspace (GSuite)
Google Workspace can act as a SAML IdP for NetSuite. In the Google Admin console, one can add a Web App > SAML for NetSuite. Google’s documentation details the process:
- Generate IdP Metadata: In Google Admin > Apps > Web and mobile apps, add an app named “NetSuite (SAML)”. In the IdP details screen, download the Google IdP metadata (Certificate and SSO URL) [53].
- Edit Service Provider Details: Google will ask for the ACS URL from NetSuite. Enter
https://<yourUniqueId>.app.netsuite.com/saml2/acs(replace with the unique NetSuite Account ID obtained from NetSuite org settings) [54]. - Attribute Mapping: Map Google directory attributes to NetSuite attributes. Google’s guide suggests:
Basic Information > Primary Email→ NetSuiteemail.NetSuite > Account ID(a custom Directory field) → NetSuiteaccount[4]. The NetSuite account ID can be stored in a Google User attribute (Admin > Directory > Users > [User] > User information) for each user, or set it as a custom field.
- Group Import (Optional): Google can send groups in SAML too (max 75 groups as claim).
- Finish on Google side.
Then in NetSuite, go to SAML Setup:
- Paste the Google SSO URL into Identity Provider Login Page [55].
- Upload the Google IdP certificate (Base64).
- Click Submit [55].
Google notes step 4 as “NetSuite as Service Provider”:
“Go to the NetSuite SAML Configuration page... enter the SSO URL you copied in Step 1. Upload the IdP certificate that you copied in Step 1. Click Submit.” [55]
The Google Admin instructions also caution about assigning the app to organizational units so only certain users can SSO [56]. This provides an end-to-end example of SAML for NetSuite with Google as IdP.
OneLogin
OneLogin has a prebuilt NetSuite SAML app. Their knowledge base guides contain similar steps:
- In OneLogin, add the NetSuite app from catalog.
- Configure SAML settings with the NetSuite SP metadata or URLs.
- Assign the app to users/groups.
A key point (from [43]): NetSuite administrators should create a NetSuite role and assign users to it before enabling SAML [57]. They must also give roles the “SAML Single Sign On” permission [58]. Then, in the SAML Setup page, copy the provided SLO endpoint and Account ID out of NetSuite (they will be needed in OneLogin) [59]. OneLogin’s docs bypass many steps by having a connector, but ultimately you supply the OneLogin metadata to NetSuite.
Ping Identity
PingIdentity (PingFederate or PingOne) is an enterprise IdP that supports SAML. There is no official guide excerpt here, but Ping’s process is analogous: create a SAML SP (NetSuite) in PingCenter, enter NetSuite’s entityID and ACS (from SP metadata), and import Ping’s IdP certificate into NetSuite. Block diagonal approach is the same. The BrokenRubik blog notes Ping as an example of “Enterprise-focused identity provider with SAML support” often used in larger orgs [18].
Custom / Other SAML Providers (ADFS, etc.)
For on-prem IdPs like ADFS, or other SAML providers (e.g. Workday, custom Shibboleth), the steps mirror above. Since there’s no built-in connector, an admin typically creates a manual SP entry and manually configures the ACS, Entity ID, and certificate based on NetSuite’s metadata [19] [1]. The general principle is the same: exchange metadata and configure agreed URLs and certificate.
Provisioning and Role Mapping
Most IdPs now support automated user provisioning (SCIM) in addition to SSO. For example, Okta and OneLogin can automatically create users in NetSuite via the REST API (if enabled) based on directory accounts [18]. While this is beyond SSO configuration, it complements SSO by pre-populating NetSuite user records and roles.
A tricky area is Role Mapping: determining which NetSuite role a user should have. By default, NetSuite logs in users to their default role if no role attribute is provided. To map IdP group membership to a NetSuite role, one can include a role attribute in the SAML assertion (Okta/ADFS can send a group-alpha claim named “role”), or use a custom SuiteScript to look up group-to-role mapping. BrokenRubik emphasizes that “role mapping… is where we see the most mistakes” in SSO setups [60]. Thus, carefully plan how user groups or OUs map to NetSuite roles and test with representative users.
Case Studies and Real-World Examples
While detailed customer case studies are often proprietary, available documentation and expert accounts provide illustrative examples of NetSuite SSO in practice:
-
Analytics Warehouse (NetSuite): Oracle’s documentation for Analytics Warehouse explicitly lists supported IdPs. It notes that NetSuite Analytics Warehouse allows SSO via both SAML and OIDC [23]. Supported SAML IdPs include Azure AD and Okta, and supported OIDC IdPs include Azure AD, Okta, and even NetSuite itself. This indicates that large-scale features in the NetSuite ecosystem rely on federated SSO with major identity platforms [23].
-
SuiteCommerce eCommerce: In SuiteCommerce (NetSuite’s e-commerce platform), some integrators have implemented custom SSO. For example, a 2025 blog by UnlockCommerce describes a scenario where NetSuite itself acted as the IdP for customer-facing webstore and portal sites [24] [25]. In this case, customers used their NetSuite credentials for all related sites. The flow: A centralized authentication service sends credential-check requests to NetSuite (via NetSuite’s web services “Validate Customer” API), and upon success issues its own token for unified access. This approach highlights NetSuite’s flexibility – it can be part of a bespoke SSO system beyond just acting as a SP.
-
Greenfield Implementation: Consider a mid-size company implementing NetSuite and Okta concurrently. The IT team enables SAML in NetSuite and configures Okta’s NetSuite application. Attribute mapping is set so that Okta provisions emails and account IDs, and maybe roles via Okta groups. Within hours, employees can sign into NetSuite using their Okta portal buttons, eliminating password resets. The company benefits from centralized MFA and user lifecycle management through Okta. Early testers praise the smoothness: “Employees click our company tile and are logged in to NetSuite immediately – no more forgotten passwords calls.” (Hypothetical anecdote, but typical benefits observed by consultants.)
-
Microsoft-Centric Enterprise: A large manufacturer using Azure AD for all apps would add NetSuite to Azure’s Enterprise Applications. After following the Azure steps, they assign Access via AD groups. Employees can then use the Office 365 panel (or myapps.microsoft.com) to launch NetSuite SSO. Admins note that group-based role assignment (via Azure’s additional claims) automatically gives field salespeople different NetSuite roles than their office colleagues [61].
These examples reflect a range of scenarios – employee SSO, customer SSO, and different IdP technologies – and all trace back to the core NetSuite SAML/OIDC configuration mechanisms detailed above.
Data Analysis and Industry Insights
SSO Adoption Trends
Enterprise Single Sign-On has become almost ubiquitous. A January 2026 SSOJet industry report (surveying 340 SaaS vendors) found that 81% of companies with over $5M ARR support SSO [20], up from 67% two years prior. The report notes, “Enterprise SSO has transformed from competitive differentiator to baseline requirement” [62]. While this survey focuses on vendors, it implies that almost all enterprise software (like NetSuite) is expected to offer SSO integration.
Parallel research by cybersecurity authorities highlights obstacles to SSO use in smaller organizations. A June 2024 CISA report points out that many SMBs have not deployed SSO due to complexity or perceived barriers [22]. The report offers recommendations, noting that vendor guidance (like this document) should help lower those barriers. For NetSuite admins, this underscores the importance of clear instructions and training when rolling out SSO.
Security Considerations
From a security standpoint, SSO mitigates password reuse and phishing risks by centralizing authentication. However, it also broadens the attack surface: if the IdP is compromised, an attacker gains NetSuite access. Both SAML and OIDC support strong security features such as signed tokens and optional encryption. Administrators should enforce Multi-Factor Authentication (MFA) at the IdP level for all NetSuite federated logins. Oracle’s warning about third-party access [11] reminds us that enabling SSO shifts trust to the IdP’s security controls.
In terms of tokens, SAML assertions are signed XML – vulnerable if attackers obtain the SP’s private key or compromise clocks (ticket timing) – but NetSuite’s implementation seems robust. OIDC uses JWTs and HTTPS; its security depends on TLS and correct validation of signatures against the OP’s JWKS. NetSuite administrators should periodically verify certificate lifetimes and ensure IdP metadata is up to date to prevent token acceptance issues.
Protocol Outlook (SAML vs OIDC)
Recent commentaries emphasize that SAML remains deeply entrenched but foresees growing OIDC adoption. A WorkOS blog (Aug 2025) explains that SAML’s rich attribute model and existing infrastructure make it “indispensable” for many enterprises, despite OIDC’s developer-friendliness [29] [21]. The same article notes the high migration cost away from SAML, stating that years of configuration and compliance around SAML assertions keep it dominant [63]. In practice, many organizations running NetSuite now support both protocols in parallel or transition gradually.
Future Directions
Looking ahead, NetSuite SSO will likely evolve along with industry trends:
-
Increased OIDC Adoption: As next-generation identity services proliferate (e.g. decentralized ID, passwordless flows), OIDC’s flexibility will be valuable. NetSuite may expand OIDC features (perhaps more user self-service flows or integrations with cloud identity services). The existence of NetSuite’s OIDC RP and even OIDC Provider (OP) roles shows Oracle’s commitment to modern identity standards [52] [23].
-
Zero Trust and Contextual Auth: Enterprises are moving toward Zero Trust models, which consider device, location, and behavior. SSO will integrate with these policies – for example, requiring re-authentication for high-risk actions in NetSuite, or conditionally allowing OIDC login only when corporate devices are used.
-
SCIM Provisioning: User provisioning (SCIM) may be adopted alongside SSO. Okta and others already offer SCIM connectors for NetSuite, automatically creating and updating user accounts and roles. As IAM evolves, expect more tight coupling between SSO, provisioning, and NetSuite’s internal role management.
-
API and Mobile SSO: NetSuite’s REST APIs and mobile apps (like NetSuite’s SuiteApp or SuiteCommerce) might leverage OIDC more. OIDC’s token model integrates easily with mobile and native apps, so future NetSuite apps may default to OIDC for mobile SSO.
-
Greater Emphasis on Security: Regulations like PCI, SOX, GDPR, etc. will continue shaping SSO. As Oracle’s documentation warns [11], enabling third-party logins means taking care that all compliance requirements are still met. Likely, Oracle will add more tools (audit logs, risk scoring) to help admins monitor SSO usage.
Ultimately, the trajectories of SAML and OIDC in NetSuite will follow overall identity trends: proven SAML systems will remain for legacy integration, while OIDC grows for new scenarios.
Conclusion
NetSuite’s support for SAML 2.0 and OpenID Connect SSO enables organizations to integrate NetSuite into their overall identity management strategy. Through careful configuration on both the NetSuite and IdP sides, administrators can achieve seamless, secure login for employees and customers alike. This report has walked through the technical details of both protocols: enabling NetSuite’s features, exchanging metadata, mapping attributes, and examples for IdPs like Okta, Azure AD, and Google Workspace. We have emphasized best practices (correct certificate formats, exact URL matching, role mapping) and highlighted authoritative guidance: for instance, managing SP metadata as per Oracle’s instructions [19] [1], or following Okta’s attribute mapping recommendations [7].
Supporting charts and tables summarize protocol differences and provider-specific steps. Notably, enabling these SSO features poses a change in your security perimeter – Oracle explicitly cautions admins to ensure the identity provider meets all security obligations [11]. As industry research shows, SSO is now a baseline requirement [20], not an optional luxury. Used properly, SSO greatly reduces user friction and potential credential theft, benefiting both IT and end-users.
Looking forward, we expect NetSuite SSO to embrace emerging identity innovations. For now, organizations should implement SAML 2.0 or OIDC (or both) according to their needs, testing thoroughly. And as one analyst notes, "SAML remains indispensable for enterprise SSO and federation” [29], while OIDC provides a modern alternative. NetSuite customers should leverage the abundant documentation and partner expertise to deliver a robust SSO integration—ensuring that their ERP ecosystem is both secure and easy to access.
Sources: Official NetSuite/Oracle documentation and industry analyses, including Oracle’s NetSuite Help Center [19] [1] [8], Okta and Azure integration guides [3] [40], Google Workspace admin documentation [4], expert blogs [14] [7] [20], and related resources. All technical claims herein are backed by citations.
External Sources
About Houseblend
HouseBlend.io is a specialist NetSuite™ consultancy built for organizations that want ERP and integration projects to accelerate growth—not slow it down. Founded in Montréal in 2019, the firm has become a trusted partner for venture-backed scale-ups and global mid-market enterprises that rely on mission-critical data flows across commerce, finance and operations. HouseBlend’s mandate is simple: blend proven business process design with deep technical execution so that clients unlock the full potential of NetSuite while maintaining the agility that first made them successful.
Much of that momentum comes from founder and Managing Partner Nicolas Bean, a former Olympic-level athlete and 15-year NetSuite veteran. Bean holds a bachelor’s degree in Industrial Engineering from École Polytechnique de Montréal and is triple-certified as a NetSuite ERP Consultant, Administrator and SuiteAnalytics User. His résumé includes four end-to-end corporate turnarounds—two of them M&A exits—giving him a rare ability to translate boardroom strategy into line-of-business realities. Clients frequently cite his direct, “coach-style” leadership for keeping programs on time, on budget and firmly aligned to ROI.
End-to-end NetSuite delivery. HouseBlend’s core practice covers the full ERP life-cycle: readiness assessments, Solution Design Documents, agile implementation sprints, remediation of legacy customisations, data migration, user training and post-go-live hyper-care. Integration work is conducted by in-house developers certified on SuiteScript, SuiteTalk and RESTlets, ensuring that Shopify, Amazon, Salesforce, HubSpot and more than 100 other SaaS endpoints exchange data with NetSuite in real time. The goal is a single source of truth that collapses manual reconciliation and unlocks enterprise-wide analytics.
Managed Application Services (MAS). Once live, clients can outsource day-to-day NetSuite and Celigo® administration to HouseBlend’s MAS pod. The service delivers proactive monitoring, release-cycle regression testing, dashboard and report tuning, and 24 × 5 functional support—at a predictable monthly rate. By combining fractional architects with on-demand developers, MAS gives CFOs a scalable alternative to hiring an internal team, while guaranteeing that new NetSuite features (e.g., OAuth 2.0, AI-driven insights) are adopted securely and on schedule.
Vertical focus on digital-first brands. Although HouseBlend is platform-agnostic, the firm has carved out a reputation among e-commerce operators who run omnichannel storefronts on Shopify, BigCommerce or Amazon FBA. For these clients, the team frequently layers Celigo’s iPaaS connectors onto NetSuite to automate fulfilment, 3PL inventory sync and revenue recognition—removing the swivel-chair work that throttles scale. An in-house R&D group also publishes “blend recipes” via the company blog, sharing optimisation playbooks and KPIs that cut time-to-value for repeatable use-cases.
Methodology and culture. Projects follow a “many touch-points, zero surprises” cadence: weekly executive stand-ups, sprint demos every ten business days, and a living RAID log that keeps risk, assumptions, issues and dependencies transparent to all stakeholders. Internally, consultants pursue ongoing certification tracks and pair with senior architects in a deliberate mentorship model that sustains institutional knowledge. The result is a delivery organisation that can flex from tactical quick-wins to multi-year transformation roadmaps without compromising quality.
Why it matters. In a market where ERP initiatives have historically been synonymous with cost overruns, HouseBlend is reframing NetSuite as a growth asset. Whether preparing a VC-backed retailer for its next funding round or rationalising processes after acquisition, the firm delivers the technical depth, operational discipline and business empathy required to make complex integrations invisible—and powerful—for the people who depend on them every day.
DISCLAIMER
This document is provided for informational purposes only. No representations or warranties are made regarding the accuracy, completeness, or reliability of its contents. Any use of this information is at your own risk. Houseblend shall not be liable for any damages arising from the use of this document. This content may include material generated with assistance from artificial intelligence tools, which may contain errors or inaccuracies. Readers should verify critical information independently. All product names, trademarks, and registered trademarks mentioned are property of their respective owners and are used for identification purposes only. Use of these names does not imply endorsement. This document does not constitute professional or legal advice. For specific guidance related to your needs, please consult qualified professionals.