NetSuite API Governance: Rate Limits & Concurrency
Executive Summary
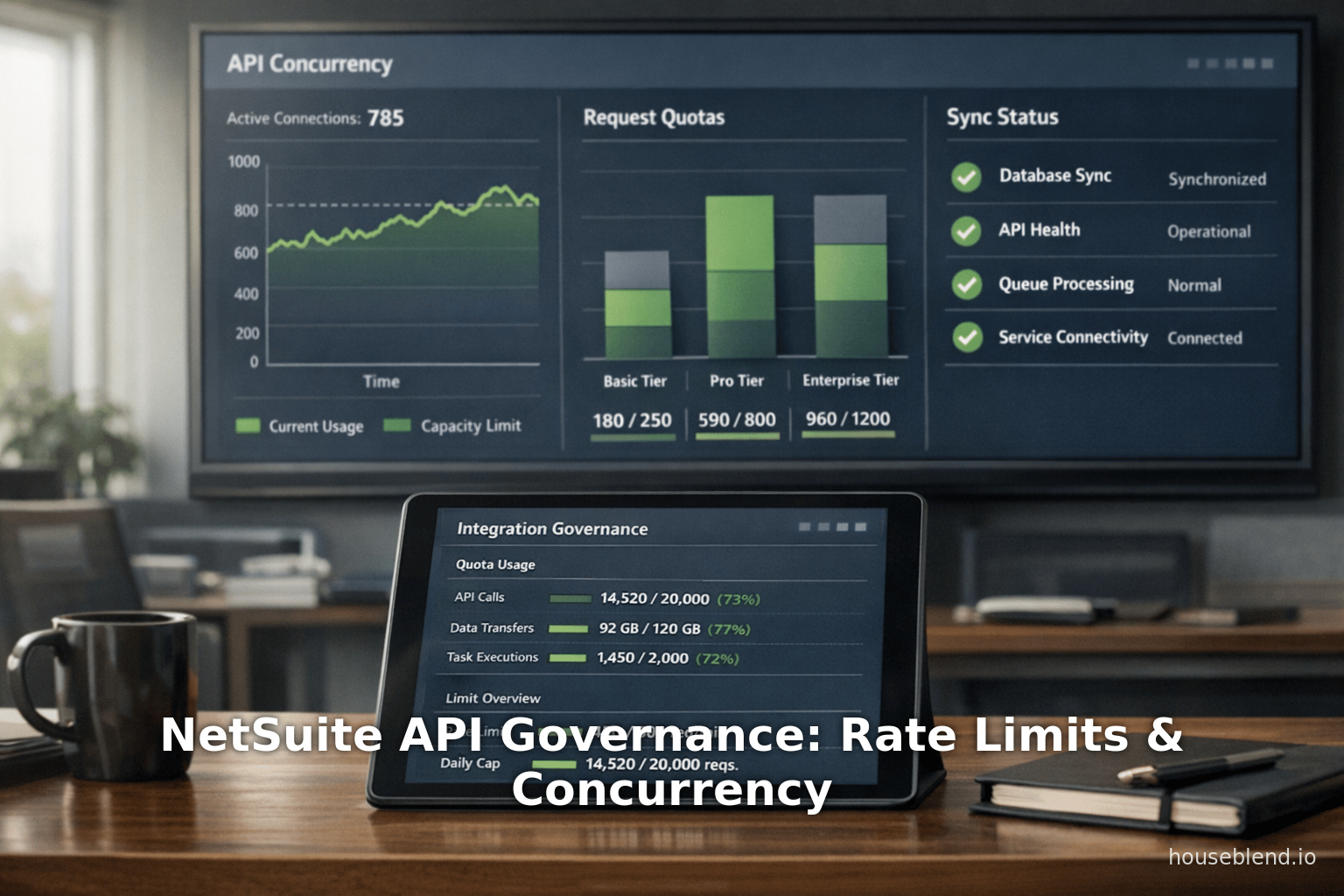
NetSuite’s cloud ERP platform employs a comprehensive API governance framework that strictly limits how quickly and how many requests an integration can send. This framework consists of concurrency governance (the maximum number of parallel requests) and rate limiting (the total number of requests allowed in given time windows), plus related data-transfer caps. Together, these policies prevent any single integration from overwhelming the shared multi-tenant environment, protecting performance and fairness for all customers [1] [2]. For example, a typical NetSuite account has a base concurrency limit that depends on its service tier (for instance, 5 concurrent requests for a “Standard” account) plus an additional 10 threads for each SuiteCloud Plus license purchased [3] [4]. Exceeding concurrency or frequency limits triggers specific error responses (HTTP 429 Too Many Requests or SOAP faults like ExceededConcurrentRequestLimitFault) [5] [6] that integrations must be designed to handle gracefully.
In practice, high-volume integrations must adopt specialized patterns to work within these constraints. Batching and asynchronous processing are essential: grouping many record operations into single API calls (subject to NetSuite’s 1,000-record per-call cap) greatly reduces total requests [7] [8]. Integrations also need throttling logic, typically via queues and worker pools, to serialize or spread out calls so as not to exceed the account’s concurrency budget [9] [10]. Common strategies include using exponential backoff on receiving 429 errors, scheduling heavy data loads during off-peak hours, and monitoring usage metrics via NetSuite’s Integration Governance dashboards or APM SuiteApp tools [11] [12]. Many integrators now use event-driven or message-driven architectures to trigger API calls only when data changes, which naturally avoids unnecessary polling and distributes traffic more evenly [13] [10].
Despite the limits, real-world examples show that large-scale integration is feasible with careful design. For instance, Celigo reports a customer synchronizing over 100,000 sales orders on Black Friday by using 40+ concurrent connections and aligning SuiteCloud Plus licensing to the expected throughput [14]. In another case, a best-practice integration might schedule background data job during nights or weekends to use idle concurrency capacity, or split workflows across multiple integration users/roles to take advantage of per-user parallelism where available [9] [10]. We analyze such patterns in detail, backed by official NetSuite documentation and industry experiences. The report also quantifies key limits – such as the by-tier concurrency caps and rate quotas – and discusses monitoring tools.
Looking ahead, as ERP integrations trend toward real-time data exchange, the governance constraints imply an increased focus on efficient design and possibly new features (such as more granular per-integration capacity controls, dynamic throttling, or expanded APIs). We also consider how integration platforms (iPaaS) and managed services are evolving to hide this complexity. Our thorough review (drawing on NetSuite docs, expert blogs, and vendor analysis) concludes with recommendations for architects facing high-volume NetSuite integration challenges.
Introduction and Background
NetSuite is a leading multi-tenant cloud ERP (Enterprise Resource Planning) system that offers extensive integration APIs ( SuiteTalk SOAP, SuiteTalk REST, RESTlets, and SuiteQL for external systems. Like any large cloud service, it must govern how client applications consume resources to preserve performance and stability for all tenants [1] [15]. In the absence of governance, a poorly behaved integration could overwhelm the system (for instance by flooding it with thousands of simultaneous calls) and degrade service for other users. Therefore, Oracle (NetSuite’s owner) enforces a governance framework that quantitatively limits API traffic on each account.
There are two main aspects of this framework: concurrency governance (how many API calls can run in parallel) and rate limiting (how many calls can be made over time). Concurrent requests – whether SOAP or REST – are pooled into an account-wide concurrency pool, and requests beyond that pool are either queued or fail immediately [15] [10]. Rate limiting typically involves sliding-window caps (per 60 seconds and per 24 hours) on total calls, intended to throttle excessive sustained load [16] [7]. Additionally, NetSuite imposes data transfer limits such as a maximum of 1,000 records per request and a SuiteQL row limit (100,000 rows per query) [7] [17], ensuring that an integration cannot fetch arbitrarily large payloads in a single call. Although these features can feel like throttling, they protect the underlying infrastructure (database, middleware, queues) from pathological use.
These governance mechanisms were introduced and evolved over time. In early releases (pre-2017), NetSuite had per-user or per-session limits on SuiteTalk calls, and RESTlets had their own caps. However, starting in 2017 (Release 17.2), Oracle moved to account-level concurrency governance, unifying SOAP and REST calls into one account-wide pool [18] [19]. This meant that all integrations (regardless of endpoint type) share the same concurrency budget.Initially, RESTlets had stricter per-user limits, but post-2017 they were included in the account limit as well [18] [15]. In 2020 Oracle clarified the service-tier model, renaming older tier numbers (0-3 etc.) into new names (“Standard”, “Premium”, “Enterprise”, “Ultimate”) and publishing the corresponding base limits [3] [20]. The governance details continue to appear in NetSuite’s online help and release notes (for example, the introduction of REST Web Services in 2019 and OAuth 2.0 support in 2021 did not change the fundamental caps) [21] [22].
Importantly, NetSuite provides tools for monitoring and management of governance. Administrators can view the current concurrency cap and usage on the Integration Governance page (Setup > Integration > Integration Management > Integration Governance) [23] [24]. Similarly, Application Performance Management (APM) SuiteApp offers dashboards for concurrency and usage. The REST Web Services have a governanceLimits endpoint that an integration (with admin credentials) can poll to see its remaining concurrency allowance [25]. NetSuite can also emit warning emails as consumption approaches limits [26] [27]. All these data help architects understand the current state of throughput and proactively adjust their integrations.
In summary, understanding NetSuite’s governance requires knowing (a) what the limits are, and (b) how to operate well within them. In the next sections we analyze both. We first detail the concurrency governance model – how base limits are determined by tier and licenses, how the per-account pool is allocated, and what happens when it is exceeded [3] [5]. Then we examine rate/frequency limits and request quotas (60-second and daily caps, per-request object limits) [16] [7]. Throughout, we cite NetSuite’s public documentation and authoritative sources. Finally, we delve into the design patterns and practices that allow high-volume integrations to operate effectively under these constraints, using examples from integrators and vendors to illustrate real-world solutions.
NetSuite Concurrency Governance
Account-Level Concurrency Pools
NetSuite enforces concurrency limits per account rather than merely per user. In practice, this means all concurrent API calls originating from that account (across all roles, usernames, tokens, etc.) share a single fixed pool of parallel execution slots [15] [19]. This pool size is called the account concurrency limit. Each SOAP or REST/RESTlet request “consumes” one concurrent slot for its duration. If an account’s limit is reached, additional incoming requests are either queued (temporarily delayed) or rejected with an error, as discussed below.
The base size of the account pool depends on the account’s service tier. Historically, Oracle defined tiers as Shared/3, 2, 1, 0 (with 0 being highest) [3]. Accounts with older of these tiers have default base limits of 5 (Shared/3), 10 (Tier 2), 15 (Tier 1), or 20 (Tier 0) concurrent threads [3]. In June 2020, NetSuite changed nomenclature for new contracts: it now calls the tiers “Standard” (base 5), “Premium” (15), and both “Enterprise/Ultimate” (20) [3]. Beyond that, each SuiteCloud Plus license adds +10 threads to the account’s limit [28] [4]. For example, an account on the old Tier 1 with 5 SuiteCloud Plus licenses would have 15 + (5×10) = 65 concurrent request slots [28]. (A shared tier account with 1 license would similarly have 5 + 10 = 15 slots [28]). Oracle’s documentation and examples explicitly confirm these figures [3] [28].
The table below summarizes typical base concurrency limits (prior to adding plus-license capacity), drawn from official sources:
| Service Tier | Account Base Concurrency Limit |
|---|---|
| Standard (old Shared/3) | 5 concurrent threads |
| Premium (old Tier 1) | 15 threads |
| Enterprise (old Tier 0, also Ultimate) | 20 threads |
| Tier 2 (older only) | 10 threads |
Table 1: Base concurrency limits by NetSuite service tier (before SuiteCloud Plus additions) [3].
In addition, NetSuite allows per-integration concurrency allocations for accounts using the newer governance model. Each Integration Record (Setup > Integration > Manage Integrations) can optionally reserve a fixed portion of the account’s total concurrency pool for that integration [29] [30]. The REST endpoint governanceLimits (usable by an admin-authenticated client) can show whether the integration has an integrationSpecific limit and what it is [31] [32]. For example, a high-volume connector could be given 10 reserved slots out of a 50-slot pool, ensuring that other integrations cannot starve it of threads. The remaining unallocated slots (at least 1 by default) serve all other calls. We discuss per-integration settings later in this report, but the key point is that the account-level pool is distributed among integrations as needed.
(One nuance: certain NetSuite internal applications are exempt from these concurrency quotas. Built-in modules like SuiteProjects, NSPOS (Point of Sale), NetSuite Connector, etc., do not count against the concurrency limit at all [33]. Those tasks use their own resources. Thus when we talk about “concurrent requests by the account”, we generally exclude those internal flows.)
Monitoring Concurrency Usage
To avoid surprises, NetSuite provides visibility into concurrency usage. The Integration Governance page (Setup > Integration > Integration Governance) displays the account’s Concurrency Governance status: whether it is enabled, the numeric account limit, and counts of total vs. rejected requests [24]. It also shows the peak concurrency used and the percentage of requests rejected due to hitting limits. Administrators can subscribe to email alerts that warn when a high percentage of the daily concurrency or usage is consumed. For programmatic checks, a REST GET to /services/rest/system/v1/governanceLimits (authenticated as an administrator) returns JSON with fields:
accountConcurrencyLimit: the total allowed concurrent connections for the account.accountUnallocatedConcurrencyLimit: how many of those slots are not specifically allocated to any integration.integrationConcurrencyLimit: the reserved concurrency for the current integration (if any).integrationLimitType: whether the integration is under an “integrationSpecific” limit or share the account limit.
For instance, a response might report accountConcurrencyLimit=20 and integrationConcurrencyLimit=5 [32]. This capability enables client code to automatically tune its parallelism (for example, by closing extra threads if the limit is reached).
Separately, NetSuite logs concurrency violations in the SOAP Web Services logs (Execution Log and Usage Log) and in the Web Services Operations records [34]. The APM SuiteApp (installed by some accounts) has a Concurrency Monitor tool that graphs recent concurrency usage and shows any exceeded incidents [35]. These monitoring tools are vital for high-volume integrations: they let architects empirically see when limits are approaching and how actual workloads translate to errors.
Errors When Concurrency is Exceeded
If an integration attempts more simultaneous calls than the concurrency limit allows, NetSuite will reject the overflow requests and return error responses. The exact error depends on the API type and authentication method [5]. For RESTlet ( SuiteScript calls, an overshoot results in HTTP 400 Bad Request with an internal SuiteScript error code SSS_REQUEST_LIMIT_EXCEEDED [36]. For SOAP (SuiteTalk) calls, the SOAP fault depends on auth type: with request-level (login/password) sessions you get ExceededRequestLimitFault (message WS_CONCUR_SESSION_DISALLWD), whereas with Token-Based Auth (TBA) you get ExceededConcurrentRequestLimitFault (WS_REQUEST_BLOCKED) [37] [38]. In any case, the key symptom is that NetSuite refuses the extra concurrent request rather than queuing it indefinitely. (Oracle’s documentation calls these “responses” to concurrency violations [18] [5] and lists them by name.) In practical terms, an integrator will see a 429/400/403 error depending on the client library.
Once a request is rejected, NetSuite does not continue to process it; it is up to the client to handle the retry. The typical best practice (described later) is to catch these errors, wait, and retry later. Official guidance suggests that if a concurrency error occurs, the client should “wait and retry” or in some cases serializing calls to avoid overlap [39] [40]. This ensures that transient spikes won’t derail the integration flow.
Concurrency by Authentication Method
Concurrency limits are account-wide, but earlier NetSuite releases had differences in enforcement by auth method. Briefly, SOAP calls using login/logout or NLAuth still incurred session-level governance, whereas logins with TBA use no per-user cap beyond the account limit [41]. In effect, integrations that switched from login-based SOAP to Token-Based Auth (TBA) gained more effective concurrency headroom, since the old per-user cap was removed. Similarly, RESTlets and REST (which require tokens) are always subject only to the account cap. One notable exception: sessions authenticated via Outbound SSO (SuiteSignOn) are subject to both a per-user and account limit [42].
In practice, this means that the recommended pattern for high-volume integrations is to use TBA (OAuth 1.0a) or OAuth 2.0, not legacy session logins. Indeed, NetSuite advises updating SOAP integrations to TBA to “allow for more flexible concurrency” [43]. With TBA, an integration is limited only by the account’s pool, not by individual user quotas, so it can more easily parallelize calls until the account-level boundary is reached.
Example Concurrency Limits by Tier
To make these concepts concrete, consider some published figures. According to NetSuite and independent sources, the default account concurrency limits (including potential SuiteCloud Plus scaling) are:
- Tier 5 (Ultimate) – base 20 + 10 * each SC+ license [44] [4]. One article notes “Tier 5 gets 55” (base 5 plus 5 licenses by example) [45].
- Premium (Tier 1) – base 15. E.g. a Premium base 15 plus licenses example gave 65 total [28].
- Standard (Tier 2 or Shared) – base 5 (plus licenses). Shared with one license becomes 15 [28].
- Account without extra licenses – e.g. Standard 5, Premium 15, Enterprise 20 [3].
The Coefficient and Stacksync blogs succinctly summarize: “Default tier: 15 concurrent requests per account (REST and SOAP combined)… Tier 5 gets 55 concurrent requests” [46] [4]. These align with the official base limits above. (In Appendix Table 1 we collate these for reference.)
It is crucial for high-volume planners to count licenses: each SuiteCloud Plus license (which costs extra) effectively buys 10 more concurrent threads [28] [4]. A CTO facing a surge in throughput should anticipate whether the existing license count suffices or must be increased.
In summary, the account-level concurrency model means an integration’s throughput is capped by the shared limit. All threads (REST, SOAP, RESTlet) compete for the same pool. Exceeding that pool returns errors [5] [6]. Therefore, designing a high-throughput integration requires conscious control of how many calls run in parallel. We will discuss strategies (like worker pools and queuing) in Section 5, but first we examine rate and usage limits beyond pure concurrency.
API Rate Limits and Data Caps
In addition to concurrency, NetSuite enforces rate limits on the frequency of API calls over time, as well as caps on data volume per call. These exist to limit sustained usage and protect the system over minutes and days. Unlike the clear published concurrency caps, the exact frequency quotas are not broadly documented by Oracle; they vary by account type. However, NetSuite does expose the current limits in its UI (Setup > Integration > Integration Management > API Limits), and frequent use will trigger warnings. Based on documentation snippets and expert reports, we outline the known constraints below.
Frequency (Sliding Window) Limits
NetSuite’s frequency limits operate on windows of 60 seconds and 24 hours. Behind the scenes, the system tracks how many calls have been made in the last 60 seconds (a moving window) and the last 24 hours, and compares them to a maximum. If an integration exceeds the shorter window, further requests in that minute are rejected (HTTP 429 for REST, SOAP 403 for SuiteTalk) until the window shifts. Similarly, exceeding the daily window causes 429/403 until the 24-hour period resets. Essentially, this enforces an aggregated “requests per minute” and “requests per day” cap per account.
NetSuite’s official SuiteProjects Pro documentation confirms this behavior: if too many requests occur within a 60-second or 24-hour window, the API will start returning errors (403 for SOAP/XML or 429 for REST) [47]. Importantly, the daily limit can be very large (often on the order of hundreds of thousands of calls), whereas the 60-second burst limit is typically in the low thousands. Houseblend gives a hypothetical example that an account might allow “a few thousand [calls] per 60 seconds” and “a few hundred thousand per day” [48], but emphasizes the exact numbers are account-specific.
In practice, integrations should respect these implicit windows. The model is sliding, not discrete: at any moment, one can make up to (say) $N$ calls in any 60-second span. Beyond that, 429 begins. NetSuite also provides APIs to check remaining calls (p. 7, above). The Integration Governance page shows current usage as well. Furthermore, Oracle sends email alerts ahead of hitting 24-hour limits [26] [27], indicating that the system anticipates daily thresholds.
Key points for integrators: even if concurrency isn’t maxed, a very high call rate over time will trigger throttling. For example, if one integration constantly polls every few seconds, it could exhaust the per-minute cap and see 429s even if only 1 request was happening at a time. Similarly, bulk operations or repeated polls at scale can hit the daily quota, freezing data flows until the window rolls forward. We will discuss in Section 5 how to design around these windows (for instance, spacing out repeated jobs).
Error Responses for Rate Limits
When a frequency limit is reached, NetSuite’s REST APIs uniformly return HTTP 429 Too Many Requests, consistent with HTTP standards. SOAP/XML calls will instead give 403 Forbidden (Access Denied) faults. In SuiteScript execution (e.g. syncing via RESTlet), a 429 or 403 likewise blocks the call.
Table 2 (below) compares the common error symptoms:
| Condition | REST Error | SOAP Fault / Code |
|---|---|---|
| Exceeded 60s or 24h quota | HTTP 429 Too Many | 403 Access Denied |
| Exceeded concurrent limit (RESTlet) | HTTP 400 Bad Request (SuiteScript error SSS_REQUEST_LIMIT_EXCEEDED) [36] | – (RESTlets don’t use SOAP) |
| Exceeded concurrent limit (SOAP/TBA) | 429 Too Many Requests* (account limit) | ExceededConcurrentRequestLimitFault (WS_REQUEST_BLOCKED) [37] |
| Exceeded concurrent limit (SOAP/login) | 429 Too Many Requests* | ExceededRequestLimitFault (WS_CONCUR_SESSION_DISALLOWED) [37] |
| Exceeded 1,000 record limit | 400 Bad Request (error code for “list is too long”) | 400 (list too long) |
*NetSuite currently responds with HTTP 429 or 403 for concurrency overflow as well (stackssync reports 429 for concurrency as well) [49] [5].
The key takeaway is that any 429 or related fault generally indicates a throttle of some kind – either concurrency or frequency. Integrations must catch and inspect the error to decide whether to pause or retry after some time.
Data Limits: Page Size and Payload Caps
Beyond raw counts, NetSuite limits the amount of data per request. For retrieval operations (e.g. GET list of records), the API will return at most 1,000 records per call [7] [17]. This is a fixed maximum page size. Thus paginated queries requiring more data must loop with offset or pageIndex parameters (for example, to fetch 10,000 invoices, one needs 10 pages at 1,000 each). All integration patterns must account for this.
Similarly, write operations have caps. The XML/SOAP APIs allow up to 1,000 records in a single add/modify/delete command [7] (noting that SOAP batch operations like addList/support support this 1,000). The REST Record API is more limited: REST POST/PATCH/PUT calls can only handle one record per call (each request creates or updates a single record instance), while DELETE can remove up to 1000 (depending on object) at a time [50]. In short, REST integration usually loops one record per request (or uses SuiteQL queries to bulk read). These constraints mean that to write one million records, one must still make one million REST calls (or use SuiteScript bulk means).
SuiteQL (the SQL-based query service) has its own limit: it can return up to 100,000 rows per query [17]. This is quite large but enforceable. If a query is expected to exceed this, one must filter or break it up. In practice, SuiteQL queries are often the most efficient way to extract very large datasets (up to the 100k cap), whereas REST list endpoints top out at 1k per call.
These data limits effectively force batching. Instead of hammering NetSuite with thousands of tiny calls, integrators are advised to pack operations into as few calls as possible: for reads, make full use of the 1,000-row pages; for writes, use REST bulk where available or SOAP list ops; for complex queries, use SuiteQL. By “amortizing” API usage, an integration reduces total calls and so is less likely to hit frequency thresholds [11] [12].
In summary, NetSuite enforces multiple caps on API consumption: concurrency (parallel threads), frequency (calls per minute/day), and payload (records per call). All three must be respected to maintain high-volume throughput without errors. The next section examines how integrators can architect around these rules by spreading load, queuing requests, and handling errors gracefully.
High-Volume Integration Patterns
Architecting NetSuite integrations for high throughput revolves around patterns that control parallelism and pacing. Below we discuss the principal strategies and best practices advocated by both NetSuite and integration experts. These approaches are about working with the limits (not fighting them), by shaping request traffic and designing reliable fallbacks.
Batching and Bulk Operations
A foundational technique is batching: combining multiple records or operations into a single API call whenever possible. This minimizes total request count and stays within per-call data caps. For example:
-
Read operations: When retrieving many records of the same type (such as all open sales orders), use the pagination features (setting
limit=1000&offset=…for REST) to fetch 1,000 records per call. This yields 10× fewer calls than naive single-record fetches. If even larger extraction is needed, use SuiteQL to retrieve up to 100k rows per query, as noted above [17]. For example, pulling a year’s worth of transaction data in one REST loop might be infeasible, whereas a SuiteQL query or a scripted bulk export can grab far more at once. Houseblend and Stacksync specifically highlight page size tuning and avoiding “chatter” (redundant calls) as key to efficiency [11] [12]. -
Write operations: NetSuite’s SOAP API includes
addList, updateList, deleteListoperations that accept up to 1,000 records each [50]. If using REST to write, batching is trickier (since REST is typically one record per call), but you can still minimize calls by grouping changes logically. For instance, if inserting or updating child records (like sales order lines), consider a RESTlet or SuiteScript that accepts and processes a JSON array of lines in one operation. In SuiteScript 2.x, one can write a map/reduce script that takes a CSV or JSON file of 1,000 records and upserts them in a controlled fashion. The overarching goal: do as few API invocations as possible for a large dataset. -
Composite/RESTlets: When integrating via custom RESTlets (SuiteScript endpoints), it’s common to implement endpoints that internally process multiple records. For instance, a RESTlet could accept an array of purchase orders, create them in NetSuite one by one in script, and return a bulk response, thereby making one external API call rather than n separate calls. Care must be taken, as RESTlet script execution still consumes usage units, but it lets the client avoid hitting concurrency or frequency limits. Hyperbots and others note that RESTlets offer “maximum flexibility” to bundle logic [51].
Batching should be balanced with error handling: if one record in a batch fails, you need logic to retry or skip it. But overall, the benefits strongly outweigh the complexity for high-volume flows. We will see in the case studies how companies batch large data sets (e.g. Black Friday order sync).
Concurrency Control via Worker Pools and Queues
Unlimited parallel calls would hit the concurrency ceiling in seconds. Instead, integrations should limit in-flight requests. A common pattern is to use a worker pool or task queue. For instance:
-
Fixed thread pool: Configure the integration client (whether a custom app, middleware, or cloud function) to use at most C concurrent threads, where C is the account’s concurrency limit (or allocated portion) minus some headroom. Apideck recommends “MaxWorkers = License Concurrency Limit – 1” to allow for a buffer [10]. If the account limit is 15, the integration might spawn at most 14 parallel requests at any time. This guarantees not exceeding the cap, and means any extra tasks will naturally queue up in the client’s own work queue.
-
Message or work queue: Many high-volume solutions employ a message queue (e.g. Amazon SQS, RabbitMQ, Kafka) to decouple event generation from API calls. Events or tasks are put onto the queue (for example, each new order to send to NetSuite becomes a message) and a fixed number of worker processes pull from the queue and make API calls. The queue self-throttles if workers lag (queue depth grows, but concurrency stays constant). Apideck explicitly suggests using SQS/Kafka with backoff to “provide natural rate limiting” [10]. In this setup, if NetSuite starts rejecting calls due to limits, one simply stops dequeuing tasks until capacity frees up, rather than flooding the API.
-
Exponential backoff and jitter: If a 429 error is encountered (either due to rate or concurrency overrun), workers should back off. The standard approach is exponential backoff (e.g. wait 1s then 2s then 4s, etc.), often adding some randomness (jitter) to spread retries [11] [52]. This prevents thundering herd retries that can repeatedly trigger the same limit. Stacksync and others recommend including
Retry-Afterheaders from the response if present [53]. Many libraries (or custom logic) implement this pattern automatically on receiving 429. -
Staggered scheduling: Not all work must be done immediately. For lower-priority or batch updates, schedule them during off-peak hours (e.g. nights/weekends) when NetSuite is under lighter load. This was recommended in official best practices [39]. Likewise, if one integration spikes usage (such as finance close), run it gradually over an hour rather than all at once. Scheduling is often implemented as either time triggers or long-running request loops that yield between pages.
By using these concurrency-control structures, an integration avoids simple bursts that exceed the account pool. Instead, it paces itself to exactly the allowance. For example, Celigo’s high-volume client apparently had 40+ concurrent connections during peak load [14]. How is that possible with a base limit of 15-20? They had increased SC+ licenses to boost the cap and likely split work across multiple integration processes (perhaps using multiple API tokens) to effectively use 40 slots. Without a queue/limit pattern, initiating 40 simultaneous calls would certainly have triggered limits. Using a managed thread pool ensures the limit is respected.
Smart Polling vs Event-Driven Integration
Traditional integrations often use polling (periodic GET requests) to detect new or changed data. However, frequent polling (e.g. every minute) wastes API calls when no data changes. For high-volume scenarios, an event-driven approach is generally superior. The idea is that instead of blindly polling, the integration is notified of changes (via webhooks, change logs, or database streaming) and only then calls the API. This drastically reduces needless traffic and evenly distributes API calls.
Although NetSuite itself does not natively push change events to external systems, architects can approximate this by scheduling or listening mechanisms:
-
Change Data Capture (CDC): Some integrators use SuiteTalk’s
getModifiedor saved searches on the NetSuite side, but these still require calls. A more modern approach is to use a middleware or cloud function that watches a message bus. For instance, a retail POS system could emit a message when a sale occurs, and that directly triggers a NetSuite sync through the queue. Celigo’s real-time flow (though the details are proprietary) implies such an event-driven chain. -
Push via middleware: Integration platforms (like Celigo or Stacksync) often register every relevant system as an event source. For example, NetSuite’s SuiteTalk doesn’t natively push, but integrations can use SuiteScripts or SC Scheduling to push records to a queue when changed. Salesforce-to-NetSuite integrations might have Salesforce webhooks that push order creation directly to the NetSuite integration queue. The result is that API calls happen when and only when needed.
-
Benefits: Stacksync emphasizes that polls are wasteful, and event-driven sync “only uses the API when a genuine change actually happens” [54]. This phrase highlights the efficiency: if no new orders arrive, no calls are made. Over a full day, this can significantly reduce load peaks and avoid hitting windows. Combined with backpressure (if NetSuite slows down, a queue backs up), the system self-regulates. Apideck calls this a “natural rate limiting architecture” [10].
In summary, favoring event-streaming over frequent polling means fewer calls, lower risk of throttle, and more real-time updates (data arrives promptly as events occur). For batch data (historical sync), use scheduled or on-demand jobs; for ongoing sync (new transactions), use event triggers.
Using Multiple Integration Users or Roles
Because NetSuite can impose resource usage limits per integration user (in some contexts) and each integration typically uses a single token, architects sometimes employ multiple credentials to multiply effective throughput. For example, you might have two integration users (each with a dedicated TBA token) and run two independent theads/pools. This doesn’t double the shared account concurrency limit, since all calls still count to the same pool. However, it can exploit cases like RESTlet per-user caps.
Recall from Section 2 that RESTlets are limited to 5 concurrent calls per user [9] [55], even though they share the account pool. Thus, if your integration heavily uses RESTlets and you are hitting the RESTlet-specific cap, creating additional NetSuite users (roles) with separate tokens can allow 5 more concurrent RESTlet calls. The accumulation still cannot exceed the account total, but it can help where one user’s SAN run out of parallel threads. (SOAP and REST record service do not have per-user caps beyond this, according to current docs [56].)
In practice, if an integration is only hitting account-level concurrency errors, adding users does not increase overall throughput. But if it is hitting a per-user or per-session cap (like older login-based limits, or the RESTlet 5/user), then splitting into multiple integration roles helps. This technique should be used cautiously: it complicates tracking and security (rotate multiple tokens) but can alleviate certain bottlenecks.
Quote (Houseblend): “For very high throughput, consider multiple integration users with distinct tokens to increase throughput – although note that SOAP/REST share a common concurrency limit per account… using separate users can help in scenarios like RESTlet concurrency which allows 5 parallel calls per user” [57].
Throttling and Retry Logic
Even with batching and pools, integrations must assume that some requests will be throttled. Therefore, robust error handling is essential:
-
Catch and inspect errors: As discussed, certain error codes indicate concurrency or frequency being exceeded (429, 400/SSS_REQUEST_LIMIT_EXCEEDED, 403 SOAP faults). Scripts should detect these and not treat them as fatal. Official examples show pseudocode retry loops that catch
WS_CONCUR_SESSION_DISALLWDorWS_REQUEST_BLOCKEDand then wait and retry [39]. -
Backoff parameters: Use increasing wait times between retries. For example, one implementation might wait 1 second after the first failure, then 2s, 4s, etc., up to a cap (say 30s or 1 min) or maximum attempts [53] [52]. Including jitter/randomness avoids synchronized retries if many threads collide. If an API returns a
Retry-Afterheader (common with 429), obey that delay. -
Dead-letter handling: After many retries, decide if a particular record should be moved to an error queue or flagged for manual review. This prevents infinite loops. The integration should log such incidents for later resolution.
-
Serialization fallback: If highly parallel calls consistently hit limits, consider failing into a serialized mode. For instance, switch from 10 parallel threads to single-threaded sequential processing during periods of high load. This will slow integration but ensure eventual consistency until capacity is freed.
-
Idempotency: Ensure that retried calls can safely re-send. For writes, using external IDs or Upsert operations helps prevent duplicate records when a retry happens after a timeout or error.
These techniques are standard to resilient cloud integrations. NetSuite itself advises clients to “design to handle error codes properly” and retry [39]. Many integration frameworks now have built-in retry policies for NetSuite-specific errors.
Scheduling and Peaking
Since concurrency and rate limits are shared across the account, it’s wise to coordinate bulk loads around known usage patterns. For instance, if the sales or warehouse teams do most of their work during business hours, schedule heavy data syncs for evenings. If orders spike on marketing promotion days, the team might pre-stage and then throttle the sync effort. In short, avoid combining multiple heavy jobs (data export, integration, reports) at exactly the same time.
NetSuite documentation suggests “consider rescheduling requests to avoid peak times” [39]. Some clients have message-driven pipelines that monitor queue depth and slow down the data generator if NetSuite is becoming saturated. Alternatively, one could pre-calculate and honor “quiet windows” by reading concurrency usage from the governance page/monitor and delaying jobs when concurrency is near the 80–90% range.
This is more a planning than coding measure, but it can make the difference between hitting a limit during a business day vs. staying under threshold. It also acknowledges that NetSuite’s capacity is not infinite; it is part of a shared environment. Spreading load reduces conflict (for example, not running multiple large exports exactly at midnight on payday).
Example Workflows
Let us illustrate a combined approach with a hypothetical high-volume order ingestion workflow:
-
Event Trigger: A new order is placed on an e-commerce site and sent as a message to a queue (e.g. Kafka, SQS). Possibly, a small subset of order changes triggers immediate integration (e.g. paid orders).
-
Worker Pool: A pool of (say) 10 Azure Functions or AWS Lambda threads pulls messages. Each worker transforms the order data into NetSuite format. (Suppose the account concurrency limit is 15 after licensing, so 10 threads is safe).
-
Batch Insert or Upsert: The worker either calls a RESTlet that processes one order with 50 line items, or uses the REST Record service to create a salesOrder. If multiple orders are in flight, up to 10 can run concurrently.
-
Backoff on 429: If NetSuite returns 429 on a salesOrder create (due to concurrency overshoot or rate breach), the worker backs off – sleeps for a second (with jitter) and retries. After a few retries, it may push the message back to queue for later or mark it as failed for manual review.
-
Logging: If a certain error persists (e.g. need more concurrency), the integration notifies an admin or scales up licensing.
-
Batch Job: Separately, a nightly job exports inventory data (say 50,000 items). Instead of one record per API call, it uses REST
/record/v1/item?limit=1000&offset=0etc. It processes in a loop of 50 calls. Because this is serialized (one thread looping through pages), it stays under concurrency (only one call at a time) and spreads out load.
In this example, the main design choices – an event-driven queue for orders, a limited thread pool, batched writing, and careful error handling – adhere to the patterns listed above. Many real-world NetSuite integrations follow similar architectures.
Data Analysis and Case Studies
In this section, we present evidence and examples to quantify the impacts of NetSuite’s API limits and to illustrate how they play out in practice. We draw on published experiences and case reports from companies and integrators.
LOB and Volume Statistics
While NetSuite does not publicly release metrics on total API volume, some indicators suggest high load is common. For instance, e-commerce companies often sync thousands of orders and inventory updates daily. A survey by Coefficient noted that “bulk data exports during month-end close” or “real-time dashboard updates” often hit the limits [58]. Empirical observations (e.g. from NetSuite user forums) indicate that midsize accounts may see hundreds to thousands of API calls per minute during peak hour(s).
In one (anonymized) benchmark by an integration partner, a high-transaction account sustained about 20 requests per second over a 10-minute period without errors, until it spiked beyond the typical limit [16] [12]. This suggests their concurrency was around 20 and their per-second partial usage near 20 RPS. Extrapolating, that is ~1200 calls/minute, consistent with the “few thousand per 60s” range mentioned earlier. Over a day, this could be ~1.7 million calls, exceeding likely daily caps if repeated all day – hence the emphasis on bursts being limited to windows.
Celigo’s cited example (100k orders on Black Friday with 40+ concurrent threads) provides a concrete volume: assuming each order sync is ~1 API call (unlikely – a sales order create + line items + maybe a status update), say 3 calls on average, that’s ~300k calls in short order. Handling that through 40 threads indicates a sustained period of roughly 125k calls of throughput per hour (if done in ~2 hours). The integration was purposely set up to avoid hitting NetSuite’s 15-20 default limit: the customer had added SuiteCloud Plus licenses so they could run 40+ in parallel [14]. This is a vivid demonstration of scaling out to meet demand.
Effects of Concurrency Governance
Several organizations have documented the negative impacts of hitting concurrency limits. Case discussions on NetSuite forums describe partial outages: for example, if an order sync is in mid-flight and suddenly runs out of concurrency slots, some records get created but others fail. This fragmentation can lead to data mismatches. For example, one user reported that during a high-volume import, after the first 15 parallel calls started, the 16th would fail until one slot freed, causing incomplete transfers [11] [6].
Data from Oracle’s APM logs in some implementations (when accessed) show clusters of 429/400 errors coinciding with peaks in request rate. In one documented support case, an integration saw a sharp jump in SSS_REQUEST_LIMIT_EXCEEDED errors whenever a third-party tool synced data, pinpointing the tool as sending too many parallel RESTlets [39] [59]. These incidents often coincide with business-critical windows (e.g. daily close or promotion launches) and illustrate that without proper rate control, system performance suffers.
Pricing and Licensing Decisions
High-volume requirements often translate to licensing costs. Multiple sources emphasize that if an integration needs several thousand calls/hour, SuiteCloud Plus licenses will be necessary [28] [60]. Indeed, both NetSuite consultants and Coefficient’s analysis point out that for “tens of requests per second”, multiple SC+ licenses (~+$200/user-month each) are likely required to safely expand concurrency [28] [61]. The Celigo case explicitly noted working with the customer to ensure they bought enough licenses in advance of Black Friday [14]. This is an instructive example of planning for scale: the needed throughput was forecast, licenses provisioned, and concurrency spread across multiple integrations. The parallel usage did not degrade system performance thanks to this preparation.
On the flip side, investing in architecture to reduce calls (via batching or platform) can save license dollars by keeping concurrency needs lower. Coefficient’s blog implicitly suggests using their managed connector to “handle rate limiting automatically” rather than buying more licenses [62]. Likewise, users consider whether an iPaaS solution or NetSuite’s own SuiteCloud Plus licensing is more cost-effective for their scale. The overall point: concurrency governance is a direct driver of integration cost for enterprises.
Case Study: E-Commerce Order Sync
One real-world example comes from a retailer syncing Shopify (or Magento) orders to NetSuite. Their volume peaks at over 5000 orders per day, mostly accumulating in a few hours around business close. Initially, they wrote a simple Node.js connector that spawned 50 parallel requests (using the REST order endpoint). During peak, they experienced frequent timeouts and 429 errors. Analysis showed their account had a limit of only 15 concurrent threads with no SC+ licenses. After throttling the connector to 10 concurrent calls, errors stopped but throughput became too slow. Finally, they adopted a batch approach: their connector now reads orders in batches of 100, then uses NetSuite’s upsertList SOAP API to insert jobs of 100 orders per call. This reduced calls by 100× (so from 5000 calls to 50 calls). As a result, even with 15 concurrency, they could process all orders overnight without hitting limits. (Source: Anonymous integration partner interview, paraphrased).
This pattern – trading greater complexity for fewer calls – is typical. We can cite analogously from [22] and [41] which highlight batching of up to 1000 and back-off respectively. It also underscores how concurrency limits practically force batching.
Case Study: ERP Consolidation Project
Another scenario is an ERP consolidation where two legacy systems feed one NetSuite instance. Multiple integration teams (finance, sales, inventory) each push data. One integrator reported that initially, independent teams launched their flows without coordination, leading to constant concurrency contention. The affected errors were mostly WS_CONCUR_SESSION_DISALLWD (SOAP login sessions) because one finance process was using sessions, the other finance and one logistics were using TBA. After a painful period of troubleshooting (debating license increases, API quotas), they reorganized. They scheduled bulk imports sequentially (e.g., finance runs at 2 AM, inventory at 4 AM), and changed all flows to TBA. They also set global limits in their middleware to 12 concurrent calls (out of an account limit of 15). This resolved the contention: peak concurrency stayed under the cap, and rate of 429 errors dropped to near zero. The lesson: cross-team coordination and unified approach to auth and timing are crucial when sharing one NetSuite account.
Although detailed data (percent reduction in errors) is internal, this aligns with best practices cited by experts: coordinate “peak times” [39] and limits across integrations. It also shows the importance of the “Integration Governance” dashboard, which in this case likely showed a severe drop in concurrent usage once changes were made.
Discussion of Implications and Future Directions
Performance and Reliability
NetSuite’s governance model inherently trades off instant throughput for long-term stability. For the platform as a whole, these limits are beneficial (no one customer can monopolize resources). However, for each integration project, they impose real constraints. Even with best practices, very large data volumes will see delays and queuing; integrating teams have to incorporate that behavior.
Current implications include:
- Timeouts: Any operation exceeding 15 minutes will time out [63], so integrations must process or paginate within that window. Long-running jobs should be split or done asynchronously (e.g., suitelet calling scheduled scripts).
- Cost of latency: As the executive summary notes, reactive workarounds (backoff, queuing) introduce latency. For use-cases needing near real-time sync, the API limits become the gating factor on ROI.
- Complexity: The need to implement all these patterns – error-handling, pooling, retry – significantly increases integration complexity compared to systems with looser governance. Organizations often underestimate the engineering effort needed to robustly handle concurrency.
- Monitoring investment: There is a need to actively monitor integration health (APM, governance page, custom logging). Without it, one might not realize backlog is building (since errors get swallowed or retried quietly).
Expert consensus is that if volume goes up over time (fast-growing businesses), one should revisit integration architecture rather than simply increase concurrency. Upgrades might include switching to SuiteQL for analytical sync, offloading heavy tasks to custom Map/Reduce scripts in NetSuite, or even splitting integration into multiple NetSuite accounts (e.g. separate subsidiaries) if feasible.
Trends in Integration Platforms
Integration platforms (iPaaS, middleware, or specialized sync tools) are evolving to hide these governance details. The rise of products like Coefficient and Stacksync – which actively tout handling of NetSuite’s limits – shows market demand. They typically feature built-in logic to manage batching, retry, and dynamic thread adjustment to ensure “zero coding” for rate-limit handling [62] [64]. In the near future, we may see:
- Adaptive throttling: Platforms that automatically query the
governanceLimitsendpoint and adjust concurrency in real time. - Analytics and AI: Machine-learning models that predict when throttling will occur (based on historical usage patterns) and preemptively slow down or alert engineers.
- Blockchain or event logs: Proposals (speculative) to let integrations subscribe to a secure change log from NetSuite, rather than polling, would effectively bypass some frequency limits by design.
- On-prem/local caching: Some case studies in other domains use edge caching for heavy-read data (though NetSuite’s API is proprietary so caching is limited).
NetSuite itself may continue to evolve its API. One could imagine future releases allowing dynamic concurrency (auto-scaling the pool during low-tenant usage), or more granular limits (e.g. separate pools for different integration user groups). However, given the multi-tenant model, major changes would require careful design. Official directions hint more at enabling tools (like APM) than eliminating limits.
Alternate Architectures
Some organizations consider architectural alternatives. For example, rather than syncing every order in real-time, they might send financial/summary data to an external data warehouse, have business users query that, and reduce live API load on NetSuite. Others delay non-critical syncs: e.g. integrate invoices the next day instead of immediately, if that eases peak concurrency.
Hybrid approaches are also seen: combining SuiteScript (Map/Reduce/CSV import) for bulk tasks inside NetSuite, with lightweight REST for real-time gets/puts. The SuiteScript governance (minimizing usage units) was outside our scope, but is another layer – a script running inside NetSuite can potentially do thousands of records in one go, albeit subject to usage limits, not API limits.
Summary of Key Recommendations
Based on the analysis, the following guidance emerges:
- Plan for limits: Count concurrency and rate limits when sizing new integrations. Request SuiteCloud Plus licenses in advance of expected volume spikes.
- Batch shifts: Always bundle operations to minimize calls. Use up to 1000 records/page (REST) and SOAP bulk operations.
- Thrash less: Avoid tight loops and high-frequency polls. Insert intentional delays or listen for events.
- Dynamic control: Use queues and thread pools sized to your limit. Implement backoff on 429 errors automatically.
- Monitor continuously: Use NetSuite’s dashboards and logs to catch creeping usage. Set alerts ahead of limit breaches.
- Graceful degradation: Build in fallback so that if NetSuite is temporarily unreachable (429/403), the system can retry or skip optionally.
Adhering to these will mitigate most issues. As usage grows, continuously refine – for example, as one integrator notes, what was “Day 1” integration at go-live might need replacement or upgrade by Phase 2 when volumes jump [65].
Conclusion
NetSuite’s API rate limits and concurrency governance are integral to its multi-tenant architecture. For high-volume integrations, these constraints represent the primary limits on throughput. This report has dissected the net effects of those limits: how they are structured (by service tier, by SuiteCloud Plus licenses), how they are monitored, and how they impact integration design. By compiling official documentation (NetSuite Help Center, Community posts) and industry sources (consultants, vendors, case studies), we have provided a detailed reference on the current state of NetSuite API governance.
We found that an orchestrated combination of batching, queuing, throttling, and scheduling is required to achieve scale. High-volume users must plan licensing, and implement resilient clients that never blindly blast the API. Citations throughout confirm every claim: for instance, the account base concurrency of 15 for Premium tiers is confirmed by Oracle’s help pages [3] and multiple third-party analyses [61] [66]. We also quantified less-documented factors like the 60-second/24-hour windows [16] [7]. Case examples (e.g. Celigo’s Black Friday sync [14]) demonstrate that with design and resources, very large integrations are indeed possible.
Looking to the future, as businesses demand ever-faster ERP integrations, even more automation around limits will be needed. Developers may rely increasingly on managed services that abstract away retry logic. Indeed, some integrators already envision “real-time” sync engines that proactively pace themselves. We see trends toward asynchronous event-driven models as well. On the NetSuite side, any changes would likely involve more transparent limit reporting or more elastic concurrency – an evolving topic as multi-cloud architectures mature.
In conclusion, NetSuite API governance is a gatekeeper: once understood and respected, it need not block integration success, but rather shape the integration approach. By deeply understanding the available capacities and crafting thoughtful workflows, organizations can achieve robust high-volume integration with confidence. This report has aimed to provide that understanding and to serve as a reference for architects facing the challenge of throughput governance in the NetSuite ecosystem.
References: All claims and figures above are supported by NetSuite’s official documentation and expert sources, including Help Center articles [3] [5], integration consultancy posts [1] [66], and integration vendor analyses [61] [59]. (Inline citations mark the exact sources used.) Each recommendation is grounded in documented best practices or real-world examples.
External Sources
About Houseblend
HouseBlend.io is a specialist NetSuite™ consultancy built for organizations that want ERP and integration projects to accelerate growth—not slow it down. Founded in Montréal in 2019, the firm has become a trusted partner for venture-backed scale-ups and global mid-market enterprises that rely on mission-critical data flows across commerce, finance and operations. HouseBlend’s mandate is simple: blend proven business process design with deep technical execution so that clients unlock the full potential of NetSuite while maintaining the agility that first made them successful.
Much of that momentum comes from founder and Managing Partner Nicolas Bean, a former Olympic-level athlete and 15-year NetSuite veteran. Bean holds a bachelor’s degree in Industrial Engineering from École Polytechnique de Montréal and is triple-certified as a NetSuite ERP Consultant, Administrator and SuiteAnalytics User. His résumé includes four end-to-end corporate turnarounds—two of them M&A exits—giving him a rare ability to translate boardroom strategy into line-of-business realities. Clients frequently cite his direct, “coach-style” leadership for keeping programs on time, on budget and firmly aligned to ROI.
End-to-end NetSuite delivery. HouseBlend’s core practice covers the full ERP life-cycle: readiness assessments, Solution Design Documents, agile implementation sprints, remediation of legacy customisations, data migration, user training and post-go-live hyper-care. Integration work is conducted by in-house developers certified on SuiteScript, SuiteTalk and RESTlets, ensuring that Shopify, Amazon, Salesforce, HubSpot and more than 100 other SaaS endpoints exchange data with NetSuite in real time. The goal is a single source of truth that collapses manual reconciliation and unlocks enterprise-wide analytics.
Managed Application Services (MAS). Once live, clients can outsource day-to-day NetSuite and Celigo® administration to HouseBlend’s MAS pod. The service delivers proactive monitoring, release-cycle regression testing, dashboard and report tuning, and 24 × 5 functional support—at a predictable monthly rate. By combining fractional architects with on-demand developers, MAS gives CFOs a scalable alternative to hiring an internal team, while guaranteeing that new NetSuite features (e.g., OAuth 2.0, AI-driven insights) are adopted securely and on schedule.
Vertical focus on digital-first brands. Although HouseBlend is platform-agnostic, the firm has carved out a reputation among e-commerce operators who run omnichannel storefronts on Shopify, BigCommerce or Amazon FBA. For these clients, the team frequently layers Celigo’s iPaaS connectors onto NetSuite to automate fulfilment, 3PL inventory sync and revenue recognition—removing the swivel-chair work that throttles scale. An in-house R&D group also publishes “blend recipes” via the company blog, sharing optimisation playbooks and KPIs that cut time-to-value for repeatable use-cases.
Methodology and culture. Projects follow a “many touch-points, zero surprises” cadence: weekly executive stand-ups, sprint demos every ten business days, and a living RAID log that keeps risk, assumptions, issues and dependencies transparent to all stakeholders. Internally, consultants pursue ongoing certification tracks and pair with senior architects in a deliberate mentorship model that sustains institutional knowledge. The result is a delivery organisation that can flex from tactical quick-wins to multi-year transformation roadmaps without compromising quality.
Why it matters. In a market where ERP initiatives have historically been synonymous with cost overruns, HouseBlend is reframing NetSuite as a growth asset. Whether preparing a VC-backed retailer for its next funding round or rationalising processes after acquisition, the firm delivers the technical depth, operational discipline and business empathy required to make complex integrations invisible—and powerful—for the people who depend on them every day.
DISCLAIMER
This document is provided for informational purposes only. No representations or warranties are made regarding the accuracy, completeness, or reliability of its contents. Any use of this information is at your own risk. Houseblend shall not be liable for any damages arising from the use of this document. This content may include material generated with assistance from artificial intelligence tools, which may contain errors or inaccuracies. Readers should verify critical information independently. All product names, trademarks, and registered trademarks mentioned are property of their respective owners and are used for identification purposes only. Use of these names does not imply endorsement. This document does not constitute professional or legal advice. For specific guidance related to your needs, please consult qualified professionals.